odbcconf.exe
- File Path:
C:\Windows\SysWOW64\odbcconf.exe - Description: ODBC Driver Configuration Program
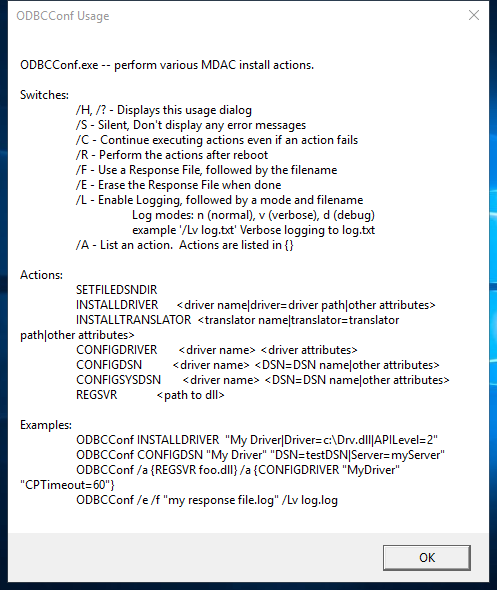
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | D567FFF92055255DBE43BF8F989A4B7E |
| SHA1 | C5062F8F0AB46D9CED9D23F1E7473338C5F24EFD |
| SHA256 | 5213C43C38D85BA69B406F27FA1A2505173DEA529010BF6DD34049E9CC9DC01A |
| SHA384 | 441A2A630E4BBBC149EC6E93156CAE6C93DBF8D8CE9D309D43F1B65E72ACC0255FFF9C4CF62C4D32B90A5F1436B4EED9 |
| SHA512 | 0A774C8D5A86C942B3B6E9E849559DCD09FE94DB8D8DA259C09787F899271A7B1037563BE5DD10941AECE4BFFA73A1DF65C3476DEA088BCED4DA86D3EC39CA82 |
| SSDEEP | 384:hVrAigT9ML8mORIdwWyjk3lxK29CnnnMrpKsOTt/v3xJPbu8dCxS9l1TlYOyvYb/:D8mOsbenq0t/7NgYbHu9Q5 |
| IMP | 0BFFB84095E2F3283A30D28326BDE550 |
| PESHA1 | 24B36B78022D48539A6CC0E647160155DE3B78D1 |
| PE256 | 4274C6FC13C3B63811E1BBEF6929F970E01AAA0C19EC9067907581E3F063F0EB |
Runtime Data
Window Title:
Invalid Parameter
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\SysWOW64\en-US\odbcconf.exe.mui | File |
| (RW-) C:\Users\user | File |
| (RW-) C:\Windows | File |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2 | Section |
| \BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\1\Windows\Theme1175649999 | Section |
| \Windows\Theme601709542 | Section |
Loaded Modules:
| Path |
|---|
| C:\Windows\SYSTEM32\ntdll.dll |
| C:\Windows\System32\wow64.dll |
| C:\Windows\System32\wow64cpu.dll |
| C:\Windows\System32\wow64win.dll |
| C:\Windows\SysWOW64\odbcconf.exe |
Signature
- Status: Signature verified.
- Serial:
3300000266BD1580EFA75CD6D3000000000266 - Thumbprint:
A4341B9FD50FB9964283220A36A1EF6F6FAA7840 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: odbcconf.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.19041.1 (WinBuild.160101.0800)
- Product Version: 10.0.19041.1
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/75
- VirusTotal Link: https://www.virustotal.com/gui/file/5213c43c38d85ba69b406f27fa1a2505173dea529010bf6dd34049e9cc9dc01a/detection
File Similarity (ssdeep match)
| File | Score |
|---|---|
| C:\Windows\SysWOW64\odbcconf.exe | 41 |
| C:\windows\SysWOW64\odbcconf.exe | 32 |
| C:\WINDOWS\SysWOW64\odbcconf.exe | 33 |
| C:\WINDOWS\SysWOW64\odbcconf.exe | 47 |
| C:\Windows\SysWOW64\odbcconf.exe | 33 |
Possible Misuse
The following table contains possible examples of odbcconf.exe being misused. While odbcconf.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_susp_odbcconf.yml | title: Application Whitelisting Bypass via DLL Loaded by odbcconf.exe |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | description: Detects defence evasion attempt via odbcconf.exe execution to load DLL |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | - https://github.com/LOLBAS-Project/LOLBAS/blob/master/yml/OSBinaries/Odbcconf.yml |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | Image\|endswith: '\odbcconf.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | ParentImage\|endswith: '\odbcconf.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | - Legitimate use of odbcconf.exe by legitimate user |
DRL 1.0 |
| LOLBAS | Odbcconf.yml | Name: Odbcconf.exe |
|
| LOLBAS | Odbcconf.yml | - Command: odbcconf -f file.rsp |
|
| LOLBAS | Odbcconf.yml | - Command: odbcconf /a {REGSVR c:\test\test.dll} |
|
| LOLBAS | Odbcconf.yml | - Path: C:\Windows\System32\odbcconf.exe |
|
| LOLBAS | Odbcconf.yml | - Path: C:\Windows\SysWOW64\odbcconf.exe |
|
| atomic-red-team | index.md | - T1218.008 Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | index.md | - Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - T1218.008 Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | | | Shortcut Modification | Valid Accounts CONTRIBUTE A TEST | Odbcconf | | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | | | Shortcut Modification | Winlogon Helper DLL | Odbcconf | | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | # T1218.008 - Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | <blockquote>Adversaries may abuse odbcconf.exe to proxy execution of malicious payloads. Odbcconf.exe is a Windows utility that allows you to configure Open Database Connectivity (ODBC) drivers and data source names.(Citation: Microsoft odbcconf.exe) Odbcconf.exe is digitally signed by Microsoft. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | Adversaries may abuse odbcconf.exe to bypass application control solutions that do not account for its potential abuse. Similar to Regsvr32, odbcconf.exe has a REGSVR flag that can be misused to execute DLLs (ex: odbcconf.exe /S /A {REGSVR "C:\Users\Public\file.dll"}). (Citation: LOLBAS Odbcconf)(Citation: TrendMicro Squiblydoo Aug 2017)(Citation: TrendMicro Cobalt Group Nov 2017) |
MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | - Atomic Test #1 - Odbcconf.exe - Execute Arbitrary DLL | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | ## Atomic Test #1 - Odbcconf.exe - Execute Arbitrary DLL | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | odbcconf.exe /S /A {REGSVR “#{dll_payload}”} | MIT License. © 2018 Red Canary |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | name: Signed Binary Execution - odbcconf |
Apache-2.0 |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | description: Leverage odbcconf for DLL injection |
Apache-2.0 |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | odbcconf.exe /S /A {REGSVR "C:\Users\Public\sandcat.dll"} |
Apache-2.0 |
MIT License. Copyright (c) 2020-2021 Strontic.