odbcconf.exe
- File Path:
C:\Windows\SysWOW64\odbcconf.exe - Description: ODBC Driver Configuration Program
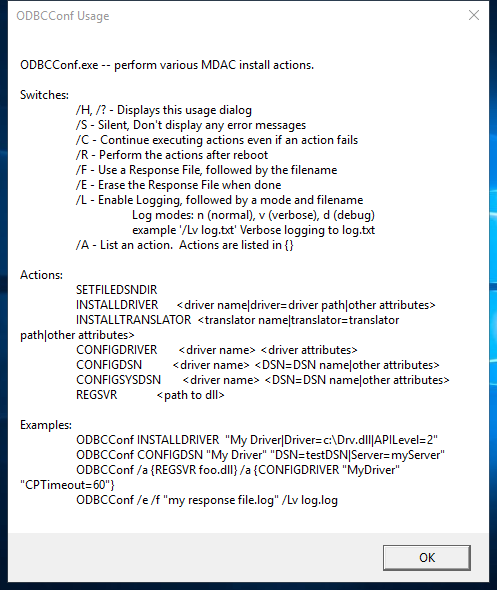
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 35CDB46FD7E96B9357D75FF285099B14 |
| SHA1 | 3DA25ACA4E86908C7FE514E53684FE52A83B0A36 |
| SHA256 | 82984508D7814CAF0E73D70ABA19359297CF23A53FF1AC891BCB84B803321858 |
| SHA384 | 3F194EA79189232CB8FF8603CB069F3FB4028FF6C062E321A8DD27186304FB9C4A6E04B8F7569788068000DD2DFACA39 |
| SHA512 | 6D2236E79932B9E6D7D88094F7A2663448AE403611925C92E7E7B94728CCD3B029963DBA286D59654FDA4D282F5A20801BAD5E2B0FEEEA8388D5EC513459609D |
| SSDEEP | 384:yVrAigT9MLuRYdwgm+E1lPK2tCnnnA2OyYOFdsvwnunVNhdpStF1a1rSCvC1yJX2:gutkmUdsHjtC1PSQygx |
| IMP | 0BFFB84095E2F3283A30D28326BDE550 |
| PESHA1 | EDF8E8BA03FC8F642F1E8EA883402ABE17F3AB8E |
| PE256 | 46894A13E488783DD7C64BC19FEBF9CBD03E7A93A577B83DCD8569BE6F6B15A8 |
Runtime Data
Window Title:
Invalid Parameter
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\SysWOW64\en-US\odbcconf.exe.mui | File |
| (RW-) C:\Users\user | File |
| (RW-) C:\Windows | File |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000004.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000004.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2.ro | Section |
| \BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\2\Windows\Theme2131664586 | Section |
| \Windows\Theme966197582 | Section |
Loaded Modules:
| Path |
|---|
| C:\Windows\SYSTEM32\ntdll.dll |
| C:\Windows\System32\wow64.dll |
| C:\Windows\System32\wow64cpu.dll |
| C:\Windows\System32\wow64win.dll |
| C:\Windows\SysWOW64\odbcconf.exe |
Signature
- Status: Signature verified.
- Serial:
33000001C422B2F79B793DACB20000000001C4 - Thumbprint:
AE9C1AE54763822EEC42474983D8B635116C8452 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: odbcconf.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.17763.1 (WinBuild.160101.0800)
- Product Version: 10.0.17763.1
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/70
- VirusTotal Link: https://www.virustotal.com/gui/file/82984508d7814caf0e73d70aba19359297cf23a53ff1ac891bcb84b803321858/detection/
File Similarity (ssdeep match)
| File | Score |
|---|---|
| C:\windows\SysWOW64\odbcconf.exe | 29 |
| C:\WINDOWS\SysWOW64\odbcconf.exe | 30 |
| C:\WINDOWS\SysWOW64\odbcconf.exe | 60 |
| C:\Windows\SysWOW64\odbcconf.exe | 40 |
| C:\Windows\SysWOW64\odbcconf.exe | 41 |
Possible Misuse
The following table contains possible examples of odbcconf.exe being misused. While odbcconf.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_susp_odbcconf.yml | title: Application Whitelisting Bypass via DLL Loaded by odbcconf.exe |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | description: Detects defence evasion attempt via odbcconf.exe execution to load DLL |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | - https://github.com/LOLBAS-Project/LOLBAS/blob/master/yml/OSBinaries/Odbcconf.yml |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | Image\|endswith: '\odbcconf.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | ParentImage\|endswith: '\odbcconf.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | - Legitimate use of odbcconf.exe by legitimate user |
DRL 1.0 |
| LOLBAS | Odbcconf.yml | Name: Odbcconf.exe |
|
| LOLBAS | Odbcconf.yml | - Command: odbcconf -f file.rsp |
|
| LOLBAS | Odbcconf.yml | - Command: odbcconf /a {REGSVR c:\test\test.dll} |
|
| LOLBAS | Odbcconf.yml | - Path: C:\Windows\System32\odbcconf.exe |
|
| LOLBAS | Odbcconf.yml | - Path: C:\Windows\SysWOW64\odbcconf.exe |
|
| atomic-red-team | index.md | - T1218.008 Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | index.md | - Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - T1218.008 Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | | | Shortcut Modification | Valid Accounts CONTRIBUTE A TEST | Odbcconf | | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | | | Shortcut Modification | Winlogon Helper DLL | Odbcconf | | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | # T1218.008 - Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | <blockquote>Adversaries may abuse odbcconf.exe to proxy execution of malicious payloads. Odbcconf.exe is a Windows utility that allows you to configure Open Database Connectivity (ODBC) drivers and data source names.(Citation: Microsoft odbcconf.exe) Odbcconf.exe is digitally signed by Microsoft. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | Adversaries may abuse odbcconf.exe to bypass application control solutions that do not account for its potential abuse. Similar to Regsvr32, odbcconf.exe has a REGSVR flag that can be misused to execute DLLs (ex: odbcconf.exe /S /A {REGSVR "C:\Users\Public\file.dll"}). (Citation: LOLBAS Odbcconf)(Citation: TrendMicro Squiblydoo Aug 2017)(Citation: TrendMicro Cobalt Group Nov 2017) |
MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | - Atomic Test #1 - Odbcconf.exe - Execute Arbitrary DLL | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | ## Atomic Test #1 - Odbcconf.exe - Execute Arbitrary DLL | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | odbcconf.exe /S /A {REGSVR “#{dll_payload}”} | MIT License. © 2018 Red Canary |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | name: Signed Binary Execution - odbcconf |
Apache-2.0 |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | description: Leverage odbcconf for DLL injection |
Apache-2.0 |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | odbcconf.exe /S /A {REGSVR "C:\Users\Public\sandcat.dll"} |
Apache-2.0 |
MIT License. Copyright (c) 2020-2021 Strontic.