osk.exe
- File Path:
C:\windows\SysWOW64\osk.exe - Description: Accessibility On-Screen Keyboard
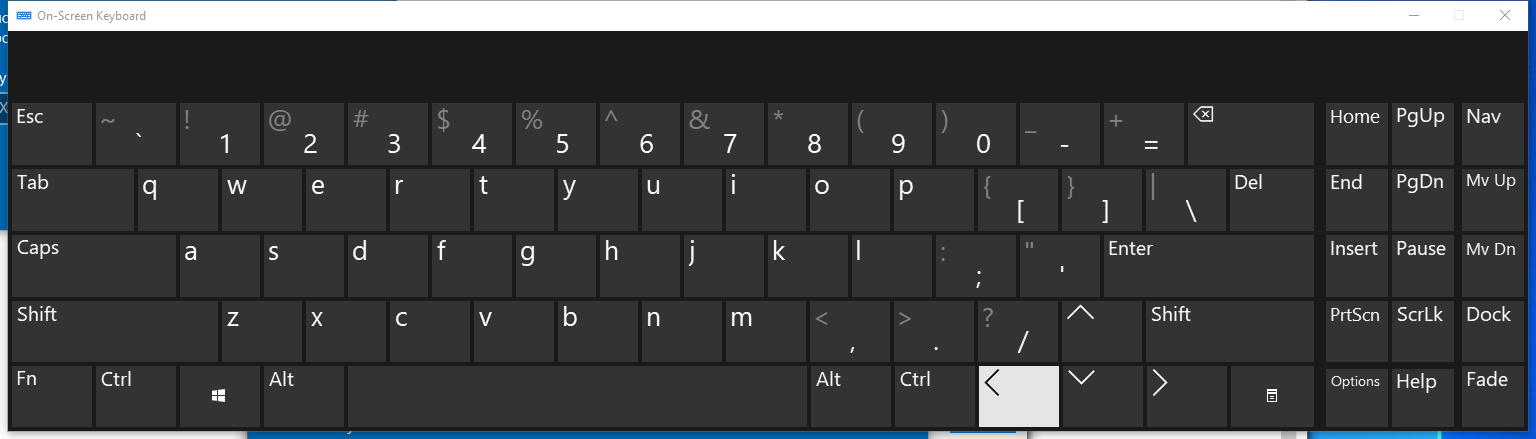
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 8519218ECB3C67B13A7CCAD4453B6012 |
| SHA1 | 169583078D52A34B18B3705E3857EF036E489684 |
| SHA256 | 556FB4023100C734B18BD59EFF82087922DEFC89845BC20F285AD2DEF7611BAB |
| SHA384 | 3CFC7A427983FEE5118D58152F83634586311CBF25548572BDB5A15EE1C6922559ED6816839802C81A5EFDB721C16821 |
| SHA512 | 8AFFE1D21FFA428F5B65C0038E43006D82C8554956CF30EB2437FD8E7606DA06136815C5F59463F5D2C1A8511FF82E1DD796C9ED00A4C96E664D24DF8C3B0632 |
| SSDEEP | 6144:gHoFAJzBoqmz5evTRboNo+CDBrH3AdKy9HGeofJgDEvr6slnCUGw/xIRLtxIRLu4:gHoCAqmzKTR0OEjmNwzaoo |
Signature
- Status: The file C:\windows\SysWOW64\osk.exe is not digitally signed. You cannot run this script on the current system. For more information about running scripts and setting execution policy, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170
- Serial: ``
- Thumbprint: ``
- Issuer:
- Subject:
File Metadata
- Original Filename: osk.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 6.3.9600.16384 (winblue_rtm.130821-1623)
- Product Version: 6.3.9600.16384
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
File Similarity (ssdeep match)
Possible Misuse
The following table contains possible examples of osk.exe being misused. While osk.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | file_event_win_uac_bypass_wmp.yml | TargetFilename: 'C:\Program Files\Windows Media Player\osk.exe' |
DRL 1.0 |
| sigma | proc_creation_win_install_reg_debugger_backdoor.yml | - 'osk.exe' |
DRL 1.0 |
| sigma | proc_creation_win_stickykey_like_backdoor.yml | - 'osk.exe' |
DRL 1.0 |
| sigma | proc_creation_win_uac_bypass_wmp.yml | Image: 'C:\Program Files\Windows Media Player\osk.exe' |
DRL 1.0 |
| sigma | registry_event_stickykey_like_backdoor.yml | - '\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osk.exe\Debugger' |
DRL 1.0 |
| sigma | registry_event_uac_bypass_wmp.yml | TargetObject\|endswith: '\SOFTWARE\Microsoft\Windows NT\CurrentVersion\AppCompatFlags\Compatibility Assistant\Store\C:\Program Files\Windows Media Player\osk.exe' |
DRL 1.0 |
| LOLBAS | Wmic.yml | - Command: wmic.exe process call create "C:\Windows\system32\reg.exe add \"HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osk.exe\" /v \"Debugger\" /t REG_SZ /d \"cmd.exe\" /f" |
|
| LOLBAS | Wmic.yml | Description: Add cmd.exe as a debugger for the osk.exe process. Each time osk.exe is run, cmd.exe will be run as well. |
|
| atomic-red-team | T1546.008.md | * On-Screen Keyboard: C:\Windows\System32\osk.exe |
MIT License. © 2018 Red Canary |
| atomic-red-team | T1546.008.md | Upon successful execution, powershell will modify the registry and swap osk.exe with cmd.exe. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1546.008.md | | parent_list | Comma separated list of system binaries to which you want to attach each #{attached_process}. Default: “osk.exe” | String | osk.exe, sethc.exe, utilman.exe, magnify.exe, narrator.exe, DisplaySwitch.exe, atbroker.exe| | MIT License. © 2018 Red Canary |
| signature-base | thor_inverse_matches.yar | description = “Abnormal osk.exe (On Screen Keyboard) - typical strings not found in file” | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | filename == “osk.exe” | CC BY-NC 4.0 |
MIT License. Copyright (c) 2020-2021 Strontic.