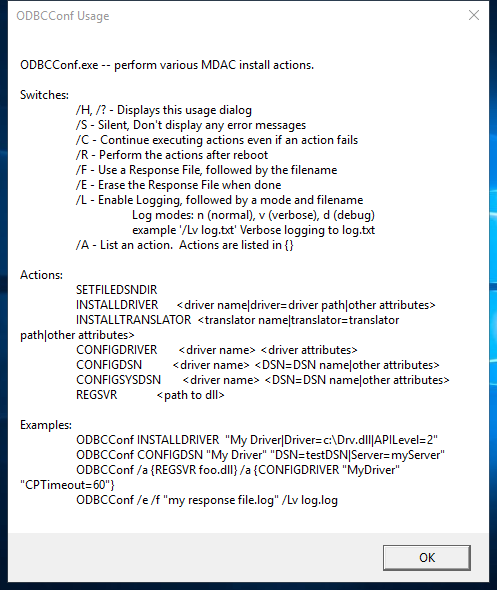
odbcconf.exe
- File Path:
C:\windows\system32\odbcconf.exe - Description: ODBC Driver Configuration Program
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | B8FF6495BED1076B1A33EF76409DBA97 |
| SHA1 | 11D594DE1BCE34EA0365D82445C571B0B013D74B |
| SHA256 | 2A39E4FCF0C717AD073104F2C6C37A39F6FEF6DB427A8BE9AA33224A5BEFC668 |
| SHA384 | 10EE3E617CB48B379431AAEDF2E23C3EBF21E073EE2C4D19DDA0E47F8107CA5557E6697BDE607D4CBD8293F6B808F33C |
| SHA512 | 2DDADBA8CFE9A70F73330B59754592CD33C8D669507662EC52E46063BCA2AE3E9F6457C8952DAE5CA1FF2E43F05150814AE4814FC584B97570EFE92F0D86CEC0 |
| SSDEEP | 384:LlrQiwD9ML3UvR2fv2LAX5qkgkHeamingjs3Do9qZBTtucoNKPwWZrW:t3Uev25kPHeaTms3DWATkSPn |
Signature
- Status: The file C:\windows\system32\odbcconf.exe is not digitally signed. You cannot run this script on the current system. For more information about running scripts and setting execution policy, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170
- Serial: ``
- Thumbprint: ``
- Issuer:
- Subject:
File Metadata
- Original Filename: odbcconf.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 6.3.9600.16384 (winblue_rtm.130821-1623)
- Product Version: 6.3.9600.16384
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
Possible Misuse
The following table contains possible examples of odbcconf.exe being misused. While odbcconf.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_susp_odbcconf.yml | title: Application Whitelisting Bypass via DLL Loaded by odbcconf.exe |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | description: Detects defence evasion attempt via odbcconf.exe execution to load DLL |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | - https://github.com/LOLBAS-Project/LOLBAS/blob/master/yml/OSBinaries/Odbcconf.yml |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | Image\|endswith: '\odbcconf.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | ParentImage\|endswith: '\odbcconf.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_odbcconf.yml | - Legitimate use of odbcconf.exe by legitimate user |
DRL 1.0 |
| LOLBAS | Odbcconf.yml | Name: Odbcconf.exe |
|
| LOLBAS | Odbcconf.yml | - Command: odbcconf -f file.rsp |
|
| LOLBAS | Odbcconf.yml | - Command: odbcconf /a {REGSVR c:\test\test.dll} |
|
| LOLBAS | Odbcconf.yml | - Path: C:\Windows\System32\odbcconf.exe |
|
| LOLBAS | Odbcconf.yml | - Path: C:\Windows\SysWOW64\odbcconf.exe |
|
| atomic-red-team | index.md | - T1218.008 Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | index.md | - Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - T1218.008 Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #1: Odbcconf.exe - Execute Arbitrary DLL [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | | | Shortcut Modification | Valid Accounts CONTRIBUTE A TEST | Odbcconf | | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | | | Shortcut Modification | Winlogon Helper DLL | Odbcconf | | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | # T1218.008 - Odbcconf | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | <blockquote>Adversaries may abuse odbcconf.exe to proxy execution of malicious payloads. Odbcconf.exe is a Windows utility that allows you to configure Open Database Connectivity (ODBC) drivers and data source names.(Citation: Microsoft odbcconf.exe) Odbcconf.exe is digitally signed by Microsoft. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | Adversaries may abuse odbcconf.exe to bypass application control solutions that do not account for its potential abuse. Similar to Regsvr32, odbcconf.exe has a REGSVR flag that can be misused to execute DLLs (ex: odbcconf.exe /S /A {REGSVR "C:\Users\Public\file.dll"}). (Citation: LOLBAS Odbcconf)(Citation: TrendMicro Squiblydoo Aug 2017)(Citation: TrendMicro Cobalt Group Nov 2017) |
MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | - Atomic Test #1 - Odbcconf.exe - Execute Arbitrary DLL | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | ## Atomic Test #1 - Odbcconf.exe - Execute Arbitrary DLL | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.008.md | odbcconf.exe /S /A {REGSVR “#{dll_payload}”} | MIT License. © 2018 Red Canary |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | name: Signed Binary Execution - odbcconf |
Apache-2.0 |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | description: Leverage odbcconf for DLL injection |
Apache-2.0 |
| stockpile | a74bc239-a196-4f7e-8d5c-fe8c0266071c.yml | odbcconf.exe /S /A {REGSVR "C:\Users\Public\sandcat.dll"} |
Apache-2.0 |
MIT License. Copyright (c) 2020-2021 Strontic.