mstsc.exe
- File Path:
C:\windows\SysWOW64\mstsc.exe - Description: Remote Desktop Connection
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 49E8FF543E23BC792A2E1D2E04608953 |
| SHA1 | 989B2B60B68FD82E2E512E02B66018D12B91782B |
| SHA256 | FD08C03D220D524E871B5FE3AD2920726A5C97D32C4525DE825220F3BBE4EE9E |
| SHA384 | C087669C57319CB842CD28AA946277D8E953821C8EA2EEEA1D8A826AF3D24DA493D60B22F3C9548CA9B91681D828D7DB |
| SHA512 | EFC1A98EA1DCE7CE8F937F8A8610D4BBE493C15222C48498D3E2FC068908502F2549F9B70231A75E849F785DECB811564E84B390A106D7BA8174ABB7407B11FF |
| SSDEEP | 12288:9cFLOV5UB7rv3FnAH2SayOoo7HOpaiUZmNJgLQgbRtUoAmyCQ28o:+ZOGvFAHROJHRiMmMMg1KA |
Signature
- Status: The file C:\windows\SysWOW64\mstsc.exe is not digitally signed. You cannot run this script on the current system. For more information about running scripts and setting execution policy, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170
- Serial: ``
- Thumbprint: ``
- Issuer:
- Subject:
File Metadata
- Original Filename: mstsc.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 6.3.9600.16384 (winblue_rtm.130821-1623)
- Product Version: 6.3.9600.16384
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
Possible Misuse
The following table contains possible examples of mstsc.exe being misused. While mstsc.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | file_event_win_tsclient_filewrite_startup.yml | Image\|endswith: '\mstsc.exe' |
DRL 1.0 |
| sigma | net_connection_win_susp_rdp.yml | - '\mstsc.exe' |
DRL 1.0 |
| sigma | proc_creation_win_mimikatz_command_line.yml | - 'mstsc' #ts module |
DRL 1.0 |
| sigma | proc_creation_win_mstsc.yml | title: Remote Desktop Protocol Use Mstsc |
DRL 1.0 |
| sigma | proc_creation_win_mstsc.yml | - https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/mstsc |
DRL 1.0 |
| sigma | proc_creation_win_mstsc.yml | Image\|endswith: \mstsc.exe |
DRL 1.0 |
| sigma | proc_creation_win_rdp_hijack_shadowing.yml | title: MSTSC Shadowing |
DRL 1.0 |
| sigma | proc_creation_win_rdp_hijack_shadowing.yml | description: Detects RDP session hijacking by using MSTSC shadowing |
DRL 1.0 |
| sigma | registry_event_mstsc_history_cleared.yml | description: Detects the deletion of registry keys containing the MSTSC connection history |
DRL 1.0 |
| atomic-red-team | T1021.001.md | mstsc /v:$Server | MIT License. © 2018 Red Canary |
| atomic-red-team | T1021.001.md | $p=Tasklist /svc /fi “IMAGENAME eq mstsc.exe” /fo csv | convertfrom-csv | MIT License. © 2018 Red Canary |
| signature-base | cn_pentestset_tools.yar | $s1 = “srv\newclient\lib\win32\obj\i386\mstsc.pdb” fullword ascii | CC BY-NC 4.0 |
| signature-base | crime_cn_campaign_njrat.yar | $a2 = “taskkill /f /im mstsc.exe” fullword ascii | CC BY-NC 4.0 |
Additional Info*
*The information below is copied from MicrosoftDocs, which is maintained by Microsoft. Available under CC BY 4.0 license.
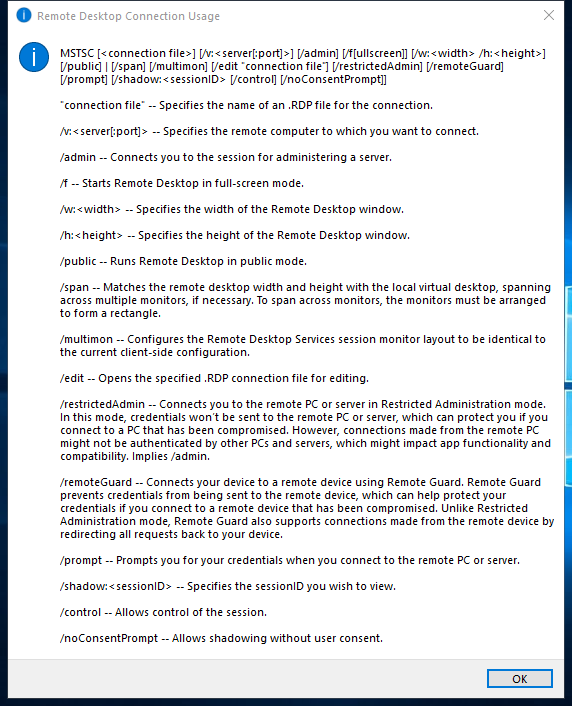
mstsc
Applies to: Windows Server 2022, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012
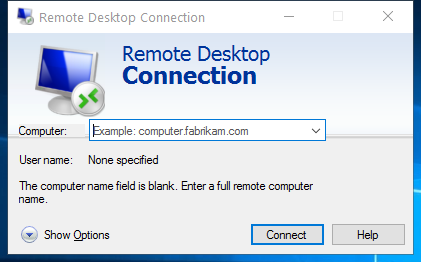
Creates connections to Remote Desktop Session Host servers or other remote computers, edits an existing Remote Desktop Connection (.rdp) configuration file, and migrates legacy connection files that were created with Client Connection Manager to new .rdp connection files.
Syntax
mstsc.exe [<connectionfile>] [/v:<server>[:<port>]] [/admin] [/f] [/w:<width> /h:<height>] [/public] [/span]
mstsc.exe /edit <connectionfile>
mstsc.exe /migrate
Parameters
| Parameter | Description |
|---|---|
<connectionfile> |
Specifies the name of an .rdp file for the connection. |
/v:<server>[:<port>] |
Specifies the remote computer and, optionally, the port number to which you want to connect. |
| /admin | Connects you to a session for administering the server. |
| /f | Starts Remote Desktop Connection in full-screen mode. |
/w:<width> |
Specifies the width of the Remote Desktop window. |
/h:<height> |
Specifies the height of the Remote Desktop window. |
| /public | Runs Remote Desktop in public mode. In public mode, passwords and bitmaps aren’t cached. |
| /span | Matches the Remote Desktop width and height with the local virtual desktop, spanning across multiple monitors if necessary. |
/edit <connectionfile> |
Opens the specified .rdp file for editing. |
| /migrate | Migrates legacy connection files that were created with Client Connection Manager to new .rdp connection files. |
| /? | Displays help at the command prompt. |
Remarks
-
Default.rdp is stored for each user as a hidden file in the user’s Documents folder.
-
User created .rdp files are saved by default in the user’s Documents folder, but can be saved anywhere.
-
To span across monitors, the monitors must use the same resolution and must be aligned horizontally (that is, side-by-side). There is currently no support for spanning multiple monitors vertically on the client system.
Examples
To connect to a session in full-screen mode, type:
mstsc /f
or
mstsc /v:computer1 /f
To assign width/height, type:
mstsc /v:computer1 /w:1920 /h:1080
To open a file called filename.rdp for editing, type:
mstsc /edit filename.rdp
Additional References
MIT License. Copyright (c) 2020-2021 Strontic.