mmc.exe
- File Path:
C:\windows\system32\mmc.exe - Description: Microsoft Management Console
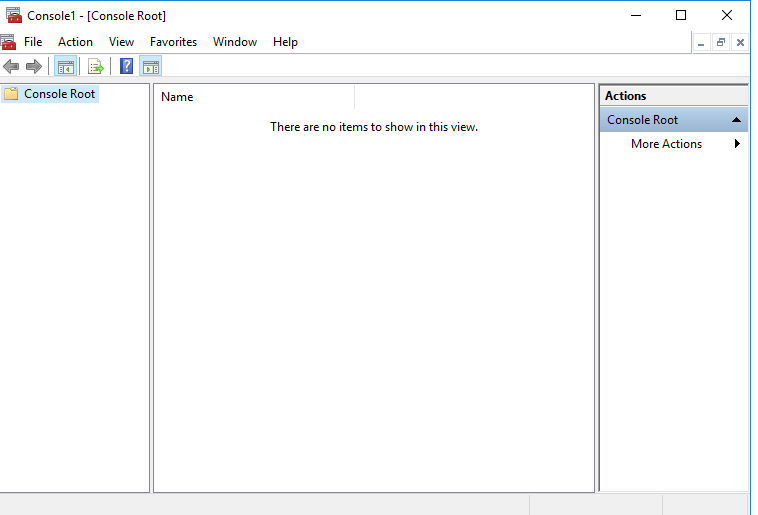
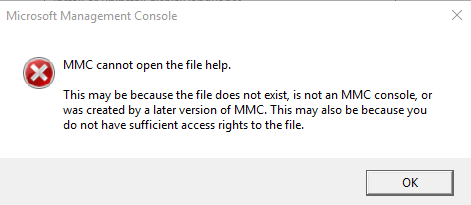
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 3E4EAD40B4F45F956354569B75FFDEEA |
| SHA1 | 059FCE23686781D12339E928D8F285ED5EFECD7C |
| SHA256 | 0CD33CC6D292D52B8C6E530158185502E47ECEF0C47D92AC7A097EF1BBCED0BC |
| SHA384 | FCD405E6EEFBC8808E2175DC277A8895ED906FCF20B983F0AC6D0B7FFBD6510DF7EE2802DDE4C66670BE7E213D81EE23 |
| SHA512 | 02719BD6E8126359707D24736EE348D348E85D6B76DDE0CA816AD0993E22A8AABDE99488DAB3A9F23A7B9087CCE99DFBA841E5EE57AE0013747B47BC64497EE5 |
| SSDEEP | 24576:HOEDdEUMCNz6RnikV2435PSKMW6r7m2UKhd0WEO9FiVMo7wMo7DH:HXdIikVr353MW6X0Khe4bU7e7DH |
Signature
- Status: The file C:\windows\system32\mmc.exe is not digitally signed. You cannot run this script on the current system. For more information about running scripts and setting execution policy, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170
- Serial: ``
- Thumbprint: ``
- Issuer:
- Subject:
File Metadata
- Original Filename: mmc.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 6.3.9600.16384 (winblue_rtm.130821-1623)
- Product Version: 6.3.9600.16384
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
File Similarity (ssdeep match)
Possible Misuse
The following table contains possible examples of mmc.exe being misused. While mmc.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | win_user_driver_loaded.yml | - '\Windows\System32\mmc.exe' |
DRL 1.0 |
| sigma | file_event_win_susp_adsi_cache_usage.yml | - 'C:\windows\system32\mmc.exe' |
DRL 1.0 |
| sigma | file_event_win_uac_bypass_dotnet_profiler.yml | description: Detects the pattern of UAC Bypass using .NET Code Profiler and mmc.exe DLL hijacking (UACMe 39) |
DRL 1.0 |
| sigma | pipe_created_susp_adfs_namedpipe_connection.yml | - '\mmc.exe' |
DRL 1.0 |
| sigma | proc_creation_win_impacket_lateralization.yml | # parent is mmc.exe |
DRL 1.0 |
| sigma | proc_creation_win_impacket_lateralization.yml | - '\mmc.exe' # dcomexec MMC |
DRL 1.0 |
| sigma | proc_creation_win_mmc20_lateral_movement.yml | description: Detects MMC20.Application Lateral Movement; specifically looks for the spawning of the parent MMC.exe with a command line of "-Embedding" as a child of svchost.exe |
DRL 1.0 |
| sigma | proc_creation_win_mmc20_lateral_movement.yml | Image\|endswith: '\mmc.exe' |
DRL 1.0 |
| sigma | proc_creation_win_mmc_spawn_shell.yml | ParentImage\|endswith: '\mmc.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | - '\mmc.exe' |
DRL 1.0 |
| sigma | proc_creation_win_sysmon_uac_bypass_eventvwr.yml | Image\|endswith: '\mmc.exe' |
DRL 1.0 |
| sigma | proc_creation_win_uac_bypass_wmp.yml | ParentCommandLine: '"C:\Windows\system32\mmc.exe" "C:\Windows\system32\eventvwr.msc" /s' |
DRL 1.0 |
| sigma | registry_event_bypass_uac_using_eventviewer.yml | Details: '%SystemRoot%\system32\mmc.exe "%1" %*' |
DRL 1.0 |
| LOLBAS | Eventvwr.yml | Description: During startup, eventvwr.exe checks the registry value HKCU\Software\Classes\mscfile\shell\open\command for the location of mmc.exe, which is used to open the eventvwr.msc saved console file. If the location of another binary or script is added to this registry value, it will be executed as a high-integrity process without a UAC prompt being displayed to the user. |
|
| LOLBAS | Eventvwr.yml | - IOC: eventvwr.exe launching child process other than mmc.exe |
|
| LOLBAS | Mmc.yml | Name: Mmc.exe |
|
| LOLBAS | Mmc.yml | - Command: mmc.exe -Embedding c:\path\to\test.msc |
|
| LOLBAS | Mmc.yml | - Command: mmc.exe gpedit.msc |
|
| LOLBAS | Mmc.yml | - Path: C:\Windows\System32\mmc.exe |
|
| LOLBAS | Mmc.yml | - Path: C:\Windows\SysWOW64\mmc.exe |
|
| LOLBAS | Wsreset.yml | - IOC: wsreset.exe launching child process other than mmc.exe |
|
| malware-ioc | nukesped_lazarus | .mmc.exe``{:.highlight .language-cmhg} |
© ESET 2014-2018 |
| atomic-red-team | T1548.002.md | copy “#{executable_binary}” “\?\C:\Windows \System32\mmc.exe” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | mklink c:\testbypass.exe “\?\C:\Windows \System32\mmc.exe” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | Target: \system32\mmc.exe | MIT License. © 2018 Red Canary |
| atomic-red-team | T1574.012.md | START MMC.EXE EVENTVWR.MSC | MIT License. © 2018 Red Canary |
| signature-base | crime_cn_campaign_njrat.yar | $a5 = “taskkill /f /im mmc.exe” fullword ascii | CC BY-NC 4.0 |
Additional Info*
*The information below is copied from MicrosoftDocs, which is maintained by Microsoft. Available under CC BY 4.0 license.
mmc
Applies to: Windows Server 2022, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012
Using mmc command-line options, you can open a specific mmc console, open mmc in author mode, or specify that the 32-bit or 64-bit version of mmc is opened.
Syntax
mmc <path>\<filename>.msc [/a] [/64] [/32]
Parameters
| Parameter | Description |
|---|---|
<path>\<filename>.msc |
starts mmc and opens a saved console. You need to specify the complete path and file name for the saved console file. If you do not specify a console file, mmc opens a new console. |
| /a | Opens a saved console in author mode. Used to make changes to saved consoles. |
| /64 | Opens the 64-bit version of mmc (mmc64). Use this option only if you are running a Microsoft 64-bit operating system and want to use a 64-bit snap-in. |
| /32 | Opens the 32-bit version of mmc (mmc32). When running a Microsoft 64-bit operating system, you can run 32-bit snap-ins by opening mmc with this command-line option when you have 32-bit only snap-ins. |
Remarks
-
You can use environment variables to create command lines or shortcuts that don’t depend on the explicit location of console files. For instance, if the path to a console file is in the system folder (for example, mmc c:\winnt\system32\console_name.msc), you can use the expandable data string %systemroot% to specify the location (mmc%systemroot%\system32\console_name.msc). This may be useful if you’re delegating tasks to people in your organization who are working on different computers.
-
When consoles are opened using the /a option, they’re opened in author mode, regardless of their default mode. This doesn’t permanently change the default mode setting for files; when you omit this option, mmc opens console files according to their default mode settings.
-
After you open mmc or a console file in author mode, you can open any existing console by clicking Open on the Console menu.
-
You can use the command line to create shortcuts for opening mmc and saved consoles. A command-line command works with the Run command on the Start menu, in any command-prompt window, in shortcuts, or in any batch file or program that calls the command.
Additional References
MIT License. Copyright (c) 2020-2021 Strontic.