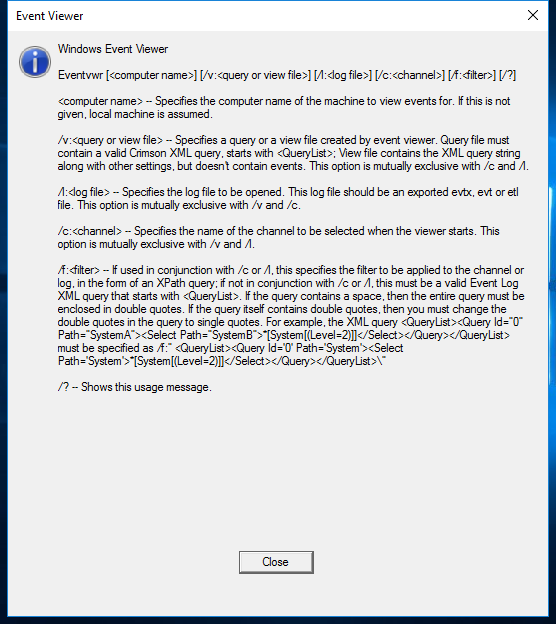
eventvwr.exe
- File Path:
C:\Windows\SysWOW64\eventvwr.exe - Description: Event Viewer Snapin Launcher
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 836D39AD5985CA36F9583D160F858D68 |
| SHA1 | 0EE97714107EC61470771F3CE93365F4A60AE6A6 |
| SHA256 | CF9149E8E5EF6F497D29C2C880A785E6B10C903355B130D1A8454D8D98E46EAE |
| SHA384 | 99A0CBED3EBB6CD94C7D33755D3CFA808D9DCFA3790F95BA98C1DE917F960B875A8B9AE6D864740D55A94CBCB45C4032 |
| SHA512 | F1E89F90E94918162BEF341A8AB38F022C5B61610F4F27EBBA27BDC34274E972D8D0C5FC5A02CCFF6EE0C3B01D91F2BB595AEF51993A5F660384DA9856E32A65 |
| SSDEEP | 1536:RMhIMfoJUhSU6nPlTggJ2oj71BgR/Vp8dY14:A3lhzslTZJ9j7Heb8C14 |
Runtime Data
Child Processes:
mmc.exe
Signature
- Status: Signature verified.
- Serial:
33000000BCE120FDD27CC8EE930000000000BC - Thumbprint:
E85459B23C232DB3CB94C7A56D47678F58E8E51E - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: eventvwr.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.14393.0 (rs1_release.160715-1616)
- Product Version: 10.0.14393.0
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
File Similarity (ssdeep match)
Possible Misuse
The following table contains possible examples of eventvwr.exe being misused. While eventvwr.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_sysmon_uac_bypass_eventvwr.yml | - https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/ |
DRL 1.0 |
| sigma | proc_creation_win_sysmon_uac_bypass_eventvwr.yml | ParentImage\|endswith: '\eventvwr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_task_folder_evasion.yml | description: The Tasks folder in system32 and syswow64 are globally writable paths. Adversaries can take advantage of this and load or influence any script hosts or ANY .NET Application in Tasks to load and execute a custom assembly into cscript, wscript, regsvr32, mshta, eventvwr |
DRL 1.0 |
| sigma | proc_creation_win_uac_bypass_wmp.yml | ParentCommandLine: '"C:\Windows\system32\mmc.exe" "C:\Windows\system32\eventvwr.msc" /s' |
DRL 1.0 |
| sigma | registry_event_bypass_uac_using_eventviewer.yml | - https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/ |
DRL 1.0 |
| sigma | registry_event_uac_bypass_eventvwr.yml | - https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/ |
DRL 1.0 |
| LOLBAS | Eventvwr.yml | Name: Eventvwr.exe |
|
| LOLBAS | Eventvwr.yml | - Command: eventvwr.exe |
|
| LOLBAS | Eventvwr.yml | Description: During startup, eventvwr.exe checks the registry value HKCU\Software\Classes\mscfile\shell\open\command for the location of mmc.exe, which is used to open the eventvwr.msc saved console file. If the location of another binary or script is added to this registry value, it will be executed as a high-integrity process without a UAC prompt being displayed to the user. |
|
| LOLBAS | Eventvwr.yml | - Path: C:\Windows\System32\eventvwr.exe |
|
| LOLBAS | Eventvwr.yml | - Path: C:\Windows\SysWOW64\eventvwr.exe |
|
| LOLBAS | Eventvwr.yml | - IOC: eventvwr.exe launching child process other than mmc.exe |
|
| LOLBAS | Eventvwr.yml | - Link: https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/ |
|
| malware-ioc | misp_invisimole.json | "description": "Windows User Account Control (UAC) allows a program to elevate its privileges to perform a task under administrator-level permissions by prompting the user for confirmation. The impact to the user ranges from denying the operation under high enforcement to allowing the user to perform the action if they are in the local administrators group and click through the prompt or allowing them to enter an administrator password to complete the action. (Citation: TechNet How UAC Works)\n\nIf the UAC protection level of a computer is set to anything but the highest level, certain Windows programs are allowed to elevate privileges or execute some elevated COM objects without prompting the user through the UAC notification box. (Citation: TechNet Inside UAC) (Citation: MSDN COM Elevation) An example of this is use of rundll32.exe to load a specifically crafted DLL which loads an auto-elevated COM object and performs a file operation in a protected directory which would typically require elevated access. Malicious software may also be injected into a trusted process to gain elevated privileges without prompting a user. (Citation: Davidson Windows) Adversaries can use these techniques to elevate privileges to administrator if the target process is unprotected.\n\nMany methods have been discovered to bypass UAC. The Github readme page for UACMe contains an extensive list of methods (Citation: Github UACMe) that have been discovered and implemented within UACMe, but may not be a comprehensive list of bypasses. Additional bypass methods are regularly discovered and some used in the wild, such as:\n\n* <code>eventvwr.exe</code> can auto-elevate and execute a specified binary or script. (Citation: enigma0x3 Fileless UAC Bypass) (Citation: Fortinet Fareit)\n\nAnother bypass is possible through some Lateral Movement techniques if credentials for an account with administrator privileges are known, since UAC is a single system security mechanism, and the privilege or integrity of a process running on one system will be unknown on lateral systems and default to high integrity. (Citation: SANS UAC Bypass)", |
© ESET 2014-2018 |
| malware-ioc | misp_invisimole.json | "https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/", |
© ESET 2014-2018 |
| atomic-red-team | T1548.002.md | * eventvwr.exe can auto-elevate and execute a specified binary or script.(Citation: enigma0x3 Fileless UAC Bypass)(Citation: Fortinet Fareit) |
MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | Bypasses User Account Control using Event Viewer and a relevant Windows Registry modification. More information here - https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/ | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | cmd.exe /c eventvwr.msc | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | PowerShell code to bypass User Account Control using Event Viewer and a relevant Windows Registry modification. More information here - https://enigma0x3.net/2016/08/15/fileless-uac-bypass-using-eventvwr-exe-and-registry-hijacking/ | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | Start-Process “C:\Windows\System32\eventvwr.msc” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1574.012.md | Write-Host “executing eventvwr.msc” -ForegroundColor Cyan | MIT License. © 2018 Red Canary |
| atomic-red-team | T1574.012.md | START MMC.EXE EVENTVWR.MSC | MIT License. © 2018 Red Canary |
| signature-base | gen_cn_hacktools.yar | $s12 = “eventvwr” fullword ascii | CC BY-NC 4.0 |
MIT License. Copyright (c) 2020-2021 Strontic.