Taskmgr.exe
- File Path:
C:\Windows\SysWOW64\Taskmgr.exe - Description: Task Manager
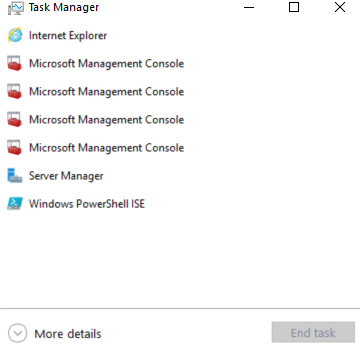
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 7941B894FA0F378B309A7427ED7A30D3 |
| SHA1 | 4606FF7C177FF2A8B456B1F95008A24584ECC88D |
| SHA256 | 4100F871176EFAA670405C7804A5ABC05E22539135A69DA811E5CA869C7579FD |
| SHA384 | 41174A9510F2AFD3A40D855BEED9C0B2E252A2C4BB301B48DA68BE2E3D00B8EDD0E28A2D569AC94B9AEAFCF885CA0D1C |
| SHA512 | 4965FB4BA36B6714C9C37DB558FF5CD8DF0D5B1744042B423EB4779E445FEB5184FE8B3C11F9FB66C39E97993DE8F83728EE101C5557E65A47A0137E2E09FFDD |
| SSDEEP | 12288:wcQ1aMYeYMcghfWVipWvHzKSg9c0fEXHpApEKyjMNga0l3KkiENgOCBxE7q4llmY:bQ19ZTcWYvzKx9c0WaL5xsgOCBe7q4GY |
Signature
- Status: Signature verified.
- Serial:
3300000266BD1580EFA75CD6D3000000000266 - Thumbprint:
A4341B9FD50FB9964283220A36A1EF6F6FAA7840 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: Taskmgr.exe
- Product Name: Task Manager
- Company Name: Microsoft Windows Operating System
- File Version: 1, 0, 0, 1
- Product Version: 1, 0, 0, 1
- Language: English (United States)
- Legal Copyright: COPYRIGHT (c) Microsoft Corporation. All rights reserved.
Possible Misuse
The following table contains possible examples of Taskmgr.exe being misused. While Taskmgr.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | win_susp_lsass_dump_generic.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | win_alert_lsass_access.yml | - 'C:\Windows\System32\Taskmgr.exe' |
DRL 1.0 |
| sigma | win_alert_lsass_access.yml | - Some Taskmgr.exe related activity |
DRL 1.0 |
| sigma | file_event_win_creation_system_file.yml | - '\Taskmgr.exe' |
DRL 1.0 |
| sigma | file_event_win_creation_system_file.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | - 'C:\WINDOWS\system32\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | # - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_lsass_memdump.yml | description: Detects process LSASS memory dump using Mimikatz, NanoDump, Invoke-Mimikatz, Procdump or Taskmgr based on the CallTrace pointing to ntdll.dll, dbghelp.dll or dbgcore.dll for win10, server2016 and up. |
DRL 1.0 |
| sigma | proc_access_win_lsass_memdump.yml | - https://blog.menasec.net/2019/02/threat-hunting-21-procdump-or-taskmgr.html |
DRL 1.0 |
| sigma | proc_access_win_susp_proc_access_lsass.yml | - 'C:\WINDOWS\system32\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_ransom_blackbyte.yml | - 'del C:\Windows\System32\Taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_spoolsv_child_processes.yml | - \taskmgr.exe |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | title: Taskmgr as LOCAL_SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | description: Detects the creation of taskmgr.exe process in context of LOCAL_SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | Image\|endswith: '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | title: Taskmgr as Parent |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | ParentImage\|endswith: '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_system_exe_anomaly.yml | - '\Taskmgr.exe' |
DRL 1.0 |
| signature-base | crime_cn_campaign_njrat.yar | $a3 = “taskkill /f /im taskmgr.exe” fullword ascii | CC BY-NC 4.0 |
| signature-base | gen_cn_hacktools.yar | $s2 = “Kiwi Taskmgr no-gpo” fullword wide | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | description = “Anomaly rule looking for certain strings in a system file (maybe false positive on certain systems) - file taskmgr.exe” | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | $s1 = “taskmgr.chm” fullword | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | ( filename == “taskmgr.exe” or filename == “Taskmgr.exe” ) and not 1 of ($s*) and not WINDOWS_UPDATE_BDC | CC BY-NC 4.0 |
MIT License. Copyright (c) 2020-2021 Strontic.