Taskmgr.exe
- File Path:
C:\WINDOWS\SysWOW64\Taskmgr.exe - Description: Task Manager
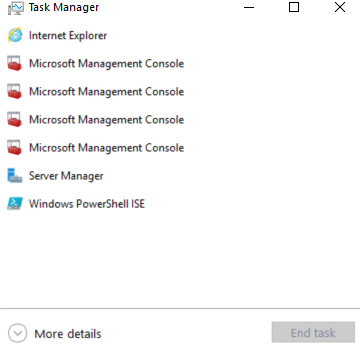
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 68C717F89D51C97F4A096D56FFE4AF95 |
| SHA1 | 229DBA8BE3292720C7938331A88AA0E4285741A9 |
| SHA256 | EFC4A6FB997C06367D39B536FA47FF1456587A8BD5AAEE74A1DA6B263674A585 |
| SHA384 | 1CCBBF8A7EFC4E660E806B1D63AF7BE7498FA3D46C7B464F42CDBB0C097994DFDF565CF46EA6FCCD13908CE5AF380729 |
| SHA512 | C040767C1CA7A86C5359A346CF7ECC0309E5A2F002D5F996E770B5C5E71BF17B1C0E5FBE782EF6CB6C710E8A7C2B88D20E41F69F736850F86312F5B3119B31FD |
| SSDEEP | 24576:6p2IEKP5hAlzL0q/1nP69ZcVAQzHgHOEALXYTmF8FO:6p2I7mF/xS9ZcVraXcXYTmeF |
| IMP | E48ED6D37AB78B890A112128172FAB3A |
| PESHA1 | 5A41BEB6AB47434B1022D5BBCC25E872B1516608 |
| PE256 | 4DA9DC4135067F53DA8ED796D114A26FA35E0522619CA53F50BCC718230F3D47 |
Runtime Data
Window Title:
Task Manager
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\System32\en-US\KernelBase.dll.mui | File |
| (R-D) C:\Windows\System32\en-US\oleaccrc.dll.mui | File |
| (R-D) C:\Windows\System32\en-US\propsys.dll.mui | File |
| (R-D) C:\Windows\System32\en-US\Taskmgr.exe.mui | File |
| (R-D) C:\Windows\SystemResources\Taskmgr.exe.mun | File |
| (RW-) C:\Windows | File |
| (RW-) C:\Windows\SysWOW64 | File |
| (RW-) C:\Windows\WinSxS\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.22000.120_none_e541a94fcce8ed6d | File |
| (RWD) C:\Users\user\AppData\Local\Microsoft\Windows\Explorer\iconcache_16.db | File |
| (RWD) C:\Users\user\AppData\Local\Microsoft\Windows\Explorer\iconcache_idx.db | File |
| \BaseNamedObjects__ComCatalogCache__ | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000001.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000001.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2.ro | Section |
| \BaseNamedObjects\windows_shell_global_counters | Section |
| \Sessions\2\BaseNamedObjects\C:*Users*user*AppData*Local*Microsoft*Windows*Caches*{3DA71D5A-20CC-432F-A115-DFE92379E91F}.3.ver0x0000000000000018.db | Section |
| \Sessions\2\BaseNamedObjects\C:*Users*user*AppData*Local*Microsoft*Windows*Caches*cversions.3.ro | Section |
| \Sessions\2\BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \Sessions\2\BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\2\BaseNamedObjects\SessionImmersiveColorPreference | Section |
| \Sessions\2\BaseNamedObjects\UrlZonesSM_TI-ADMIN | Section |
| \Sessions\2\BaseNamedObjects\windows_shell_global_counters | Section |
| \Sessions\2\Windows\Theme1077709572 | Section |
| \Windows\Theme3461253685 | Section |
Loaded Modules:
| Path |
|---|
| C:\WINDOWS\SYSTEM32\ntdll.dll |
| C:\WINDOWS\System32\wow64.dll |
| C:\WINDOWS\System32\wow64base.dll |
| C:\WINDOWS\System32\wow64con.dll |
| C:\WINDOWS\System32\wow64win.dll |
| C:\WINDOWS\SysWOW64\Taskmgr.exe |
Signature
- Status: Signature verified.
- Serial:
33000002ED2C45E4C145CF48440000000002ED - Thumbprint:
312860D2047EB81F8F58C29FF19ECDB4C634CF6A - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: Taskmgr.exe
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.22000.65 (WinBuild.160101.0800)
- Product Version: 10.0.22000.65
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/73
- VirusTotal Link: https://www.virustotal.com/gui/file/efc4a6fb997c06367d39b536fa47ff1456587a8bd5aaee74a1da6b263674a585/detection
Possible Misuse
The following table contains possible examples of Taskmgr.exe being misused. While Taskmgr.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | win_susp_lsass_dump_generic.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | win_alert_lsass_access.yml | - 'C:\Windows\System32\Taskmgr.exe' |
DRL 1.0 |
| sigma | win_alert_lsass_access.yml | - Some Taskmgr.exe related activity |
DRL 1.0 |
| sigma | file_event_win_creation_system_file.yml | - '\Taskmgr.exe' |
DRL 1.0 |
| sigma | file_event_win_creation_system_file.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | - 'C:\WINDOWS\system32\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | # - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_lsass_memdump.yml | description: Detects process LSASS memory dump using Mimikatz, NanoDump, Invoke-Mimikatz, Procdump or Taskmgr based on the CallTrace pointing to ntdll.dll, dbghelp.dll or dbgcore.dll for win10, server2016 and up. |
DRL 1.0 |
| sigma | proc_access_win_lsass_memdump.yml | - https://blog.menasec.net/2019/02/threat-hunting-21-procdump-or-taskmgr.html |
DRL 1.0 |
| sigma | proc_access_win_susp_proc_access_lsass.yml | - 'C:\WINDOWS\system32\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_ransom_blackbyte.yml | - 'del C:\Windows\System32\Taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_spoolsv_child_processes.yml | - \taskmgr.exe |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | title: Taskmgr as LOCAL_SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | description: Detects the creation of taskmgr.exe process in context of LOCAL_SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | Image\|endswith: '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | title: Taskmgr as Parent |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | ParentImage\|endswith: '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_system_exe_anomaly.yml | - '\Taskmgr.exe' |
DRL 1.0 |
| signature-base | crime_cn_campaign_njrat.yar | $a3 = “taskkill /f /im taskmgr.exe” fullword ascii | CC BY-NC 4.0 |
| signature-base | gen_cn_hacktools.yar | $s2 = “Kiwi Taskmgr no-gpo” fullword wide | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | description = “Anomaly rule looking for certain strings in a system file (maybe false positive on certain systems) - file taskmgr.exe” | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | $s1 = “taskmgr.chm” fullword | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | ( filename == “taskmgr.exe” or filename == “Taskmgr.exe” ) and not 1 of ($s*) and not WINDOWS_UPDATE_BDC | CC BY-NC 4.0 |
MIT License. Copyright (c) 2020-2021 Strontic.