Taskmgr.exe
- File Path:
C:\Windows\system32\Taskmgr.exe - Description: Task Manager
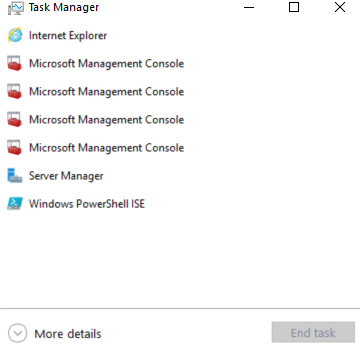
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 58D5BC7895F7F32EE308E34F06F25DD5 |
| SHA1 | 7A7F5E991DDEAF73E15A0FDCB5C999C0248A2FA4 |
| SHA256 | 4E305198F15BAFD5728B5FB8E7FF48D9F312399C744ECFEA0ECAC79D93C5E478 |
| SHA384 | 3FBB64E9070F0D14AACC654A4760864F2458122EE404ECFE9F84094F0366081885E91176938683492C74E67DD9720DEC |
| SHA512 | 872C84C92B0E4050AE4A4137330EC3CDA30008FD15D6413BF7A913C03A021AD41B6131E5A7356B374CED98D37AE207147EBEFD93893560DC15C3E9875F93F7A9 |
| SSDEEP | 24576:8aJYRVlP7OdDl8eA3fLEf4BTXasTSL/BvWac7j21dpzoQ7:h8CdDly3fL9BRSL/Bj+j21dpZ7 |
| IMP | E0B20B2FFB8E5455773387F528CDDA26 |
| PESHA1 | 9BA18ACE4126838DD39E1E05A1D7EC7423F281C1 |
| PE256 | 1F425EA74C2C222EACE585E9A6C6312FA71AF2122E3479293B9017FE22916CC0 |
Runtime Data
Window Title:
Task Manager
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\apppatch\DirectXApps_FOD.sdb | File |
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\System32\en-US\oleaccrc.dll.mui | File |
| (R-D) C:\Windows\System32\en-US\Taskmgr.exe.mui | File |
| (R-D) C:\Windows\SystemResources\Taskmgr.exe.mun | File |
| (RW-) C:\Users\user | File |
| (RW-) C:\Windows\WinSxS\amd64_microsoft.windows.common-controls_6595b64144ccf1df_6.0.19041.1110_none_60b5254171f9507e | File |
| (RWD) C:\Users\user\AppData\Local\Microsoft\Windows\Explorer\iconcache_16.db | File |
| (RWD) C:\Users\user\AppData\Local\Microsoft\Windows\Explorer\iconcache_idx.db | File |
| \BaseNamedObjects__ComCatalogCache__ | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000002.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2 | Section |
| \BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\1\BaseNamedObjects\C:*Users*user*AppData*Local*Microsoft*Windows*Caches*{3DA71D5A-20CC-432F-A115-DFE92379E91F}.3.ver0x0000000000000022.db | Section |
| \Sessions\1\BaseNamedObjects\C:*Users*user*AppData*Local*Microsoft*Windows*Caches*cversions.3.ro | Section |
| \Sessions\1\BaseNamedObjects\SessionImmersiveColorPreference | Section |
| \Sessions\1\BaseNamedObjects\windows_shell_global_counters | Section |
| \Sessions\1\Windows\Theme449731986 | Section |
| \Windows\Theme1396518710 | Section |
Loaded Modules:
| Path |
|---|
| C:\Windows\System32\combase.dll |
| C:\Windows\System32\KERNEL32.DLL |
| C:\Windows\System32\KERNELBASE.dll |
| C:\Windows\System32\msvcp_win.dll |
| C:\Windows\SYSTEM32\ntdll.dll |
| C:\Windows\System32\OLEAUT32.dll |
| C:\Windows\SYSTEM32\powrprof.dll |
| C:\Windows\System32\RPCRT4.dll |
| C:\Windows\system32\Taskmgr.exe |
| C:\Windows\System32\ucrtbase.dll |
Signature
- Status: Signature verified.
- Serial:
33000002EC6579AD1E670890130000000002EC - Thumbprint:
F7C2F2C96A328C13CDA8CDB57B715BDEA2CBD1D9 - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: Taskmgr.exe.mui
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.19041.1202 (WinBuild.160101.0800)
- Product Version: 10.0.19041.1202
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 64-bit
File Scan
- VirusTotal Detections: 0/73
- VirusTotal Link: https://www.virustotal.com/gui/file/4e305198f15bafd5728b5fb8e7ff48d9f312399c744ecfea0ecac79d93c5e478/detection
Possible Misuse
The following table contains possible examples of Taskmgr.exe being misused. While Taskmgr.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | win_susp_lsass_dump_generic.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | win_alert_lsass_access.yml | - 'C:\Windows\System32\Taskmgr.exe' |
DRL 1.0 |
| sigma | win_alert_lsass_access.yml | - Some Taskmgr.exe related activity |
DRL 1.0 |
| sigma | file_event_win_creation_system_file.yml | - '\Taskmgr.exe' |
DRL 1.0 |
| sigma | file_event_win_creation_system_file.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | - 'C:\WINDOWS\system32\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | # - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_access_win_lsass_memdump.yml | description: Detects process LSASS memory dump using Mimikatz, NanoDump, Invoke-Mimikatz, Procdump or Taskmgr based on the CallTrace pointing to ntdll.dll, dbghelp.dll or dbgcore.dll for win10, server2016 and up. |
DRL 1.0 |
| sigma | proc_access_win_lsass_memdump.yml | - https://blog.menasec.net/2019/02/threat-hunting-21-procdump-or-taskmgr.html |
DRL 1.0 |
| sigma | proc_access_win_susp_proc_access_lsass.yml | - 'C:\WINDOWS\system32\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_ransom_blackbyte.yml | - 'del C:\Windows\System32\Taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_spoolsv_child_processes.yml | - \taskmgr.exe |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | title: Taskmgr as LOCAL_SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | description: Detects the creation of taskmgr.exe process in context of LOCAL_SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_localsystem.yml | Image\|endswith: '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | title: Taskmgr as Parent |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | ParentImage\|endswith: '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_susp_taskmgr_parent.yml | - '\taskmgr.exe' |
DRL 1.0 |
| sigma | proc_creation_win_system_exe_anomaly.yml | - '\Taskmgr.exe' |
DRL 1.0 |
| signature-base | crime_cn_campaign_njrat.yar | $a3 = “taskkill /f /im taskmgr.exe” fullword ascii | CC BY-NC 4.0 |
| signature-base | gen_cn_hacktools.yar | $s2 = “Kiwi Taskmgr no-gpo” fullword wide | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | description = “Anomaly rule looking for certain strings in a system file (maybe false positive on certain systems) - file taskmgr.exe” | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | $s1 = “taskmgr.chm” fullword | CC BY-NC 4.0 |
| signature-base | thor_inverse_matches.yar | ( filename == “taskmgr.exe” or filename == “Taskmgr.exe” ) and not 1 of ($s*) and not WINDOWS_UPDATE_BDC | CC BY-NC 4.0 |
MIT License. Copyright (c) 2020-2021 Strontic.