Installer.exe
- File Path:
C:\Program Files (x86)\Zoom\bin\Installer.exe - Description: Zoom Installer
- Comments: Zoom Installer
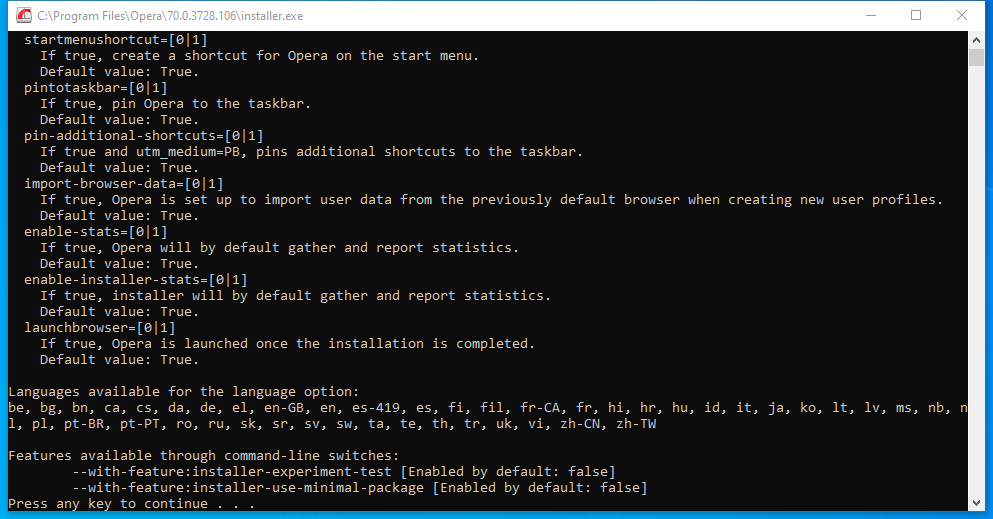
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | A7ED81AEE36EB3A2EC7DF29D6AA19C2F |
| SHA1 | F1D41FA5962E3D89BC5D979071CD15F15872A9ED |
| SHA256 | 079D617A8F224F0C925DB9FA599A0ED2D13F413CEDDBA8CF1EAFC0DCE580EA4B |
| SHA384 | BF4798727E3B9C9611D2761FC6BF555AEDA65D6185B4072D81A40CAC3766594F0310DD37E8BD714A90B275F053FDF6F6 |
| SHA512 | 5772C9AA59D4834A1175CECC35752F63A19298D54E4FA8E6D1C1CF2DF0D615AB8AFE9245E94B3D77FBE96F99A2BDB834179515D8AF0CF4C61AA789A588344845 |
| SSDEEP | 12288:uCCOOkTIHIMovI8Ve1UdjoCriCK51iruX7/u6ReSrdtZ2U20BQQI:uCCOhIJF8Ve1UqCUHR7tb207I |
| IMP | 6025EE0BF5CB4FB8CE5F938CC4AE9EEC |
| PESHA1 | 2ABD7060989C9621F3D78D14A007E29644C85F4A |
| PE256 | 42A8080F8E14BE3653D6E827A58644627CB7B23F4EF98DC44D14BF77CF557224 |
Runtime Data
Child Processes:
Zoom.exe
Loaded Modules:
| Path |
|---|
| C:\Program Files (x86)\Zoom\bin\Installer.exe |
| C:\Windows\SYSTEM32\ntdll.dll |
| C:\Windows\System32\wow64.dll |
| C:\Windows\System32\wow64cpu.dll |
| C:\Windows\System32\wow64win.dll |
Signature
- Status: Signature verified.
- Serial:
0510C6B2FF7AB71C786EF572239B1243 - Thumbprint:
0F9ADA46756C17EFFFD467D10654E2A766566CB3 - Issuer: CN=DigiCert EV Code Signing CA (SHA2), OU=www.digicert.com, O=DigiCert Inc, C=US
- Subject: CN=”Zoom Video Communications, Inc.”, O=”Zoom Video Communications, Inc.”, L=San Jose, S=California, C=US, SERIALNUMBER=4969967, OID.2.5.4.15=Private Organization, OID.1.3.6.1.4.1.311.60.2.1.2=Delaware, OID.1.3.6.1.4.1.311.60.2.1.3=US
File Metadata
- Original Filename: Zoom Installer
- Product Name: Zoom Installer
- Company Name: Zoom Video Communications, Inc.
- File Version: 5,3,52670,0921
- Product Version: 5,3,52670,0921
- Language: English (United States)
- Legal Copyright: Zoom Video Communications, Inc. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/71
- VirusTotal Link: https://www.virustotal.com/gui/file/079d617a8f224f0c925db9fa599a0ed2d13f413ceddba8cf1eafc0dce580ea4b/detection/
Possible Misuse
The following table contains possible examples of Installer.exe being misused. While Installer.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | win_alert_lsass_access.yml | - 'C:\WINDOWS\Installer\' |
DRL 1.0 |
| sigma | image_load_suspicious_dbghelp_dbgcore_load.yml | # - '\msiexec.exe' an installer installing a program using one of those DLL will raise an alert |
DRL 1.0 |
| sigma | net_connection_win_msiexec.yml | Msiexec.exe is the command-line utility for the Windows Installer and is thus commonly associated with executing installation packages (.msi) |
DRL 1.0 |
| sigma | proc_access_win_cmstp_execution_by_access.yml | description: Detects various indicators of Microsoft Connection Manager Profile Installer execution |
DRL 1.0 |
| sigma | proc_access_win_cred_dump_lsass_access.yml | SourceImage\|endswith: \Installer\setup.exe |
DRL 1.0 |
| sigma | proc_creation_win_always_install_elevated_msi_spawned_cmd_powershell.yml | description: This rule looks for Windows Installer service (msiexec.exe) spawned command line and/or powershell |
DRL 1.0 |
| sigma | proc_creation_win_always_install_elevated_msi_spawned_cmd_powershell.yml | - '\Windows\Installer\' |
DRL 1.0 |
| sigma | proc_creation_win_always_install_elevated_windows_installer.yml | title: Always Install Elevated Windows Installer |
DRL 1.0 |
| sigma | proc_creation_win_always_install_elevated_windows_installer.yml | description: This rule looks for Windows Installer service (msiexec.exe) trying to install MSI packages with SYSTEM privilege |
DRL 1.0 |
| sigma | proc_creation_win_always_install_elevated_windows_installer.yml | - '\Windows\Installer\' |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_com_object_access.yml | description: Detects UAC Bypass Attempt Using Microsoft Connection Manager Profile Installer Autoelevate-capable COM Objects (e.g. UACMe ID of 41, 43, 58 or 65) |
DRL 1.0 |
| sigma | proc_creation_win_cmstp_execution_by_creation.yml | description: Detects various indicators of Microsoft Connection Manager Profile Installer execution |
DRL 1.0 |
| sigma | proc_creation_win_msiexec_execute_dll.yml | Msiexec.exe is the command-line utility for the Windows Installer and is thus commonly associated with executing installation packages (.msi) |
DRL 1.0 |
| sigma | proc_creation_win_msiexec_install_quiet.yml | Msiexec.exe is the command-line utility for the Windows Installer and is thus commonly associated with executing installation packages (.msi) |
DRL 1.0 |
| sigma | proc_creation_win_susp_disable_eventlog.yml | - Installer tools that disable services, e.g. before log collection agent installation |
DRL 1.0 |
| sigma | proc_creation_win_susp_disable_ie_features.yml | - Unknown, maybe some security software installer disables these features temporarily |
DRL 1.0 |
| sigma | proc_creation_win_susp_instalutil.yml | - https://docs.microsoft.com/en-us/dotnet/framework/tools/installutil-exe-installer-tool |
DRL 1.0 |
| sigma | proc_creation_win_susp_msiexec_web_install.yml | - https://blog.trendmicro.com/trendlabs-security-intelligence/attack-using-windows-installer-msiexec-exe-leads-lokibot/ |
DRL 1.0 |
| sigma | proc_creation_win_susp_non_exe_image.yml | Image\|startswith: 'C:\Windows\Installer\MSI' |
DRL 1.0 |
| sigma | proc_creation_win_susp_razorinstaller_explorer.yml | description: Detects a explorer.exe sub process of the RazerInstaller software which can be invoked from the installer to select a different installation folder but can also be exploited to escalate privileges to LOCAL SYSTEM |
DRL 1.0 |
| sigma | proc_creation_win_susp_razorinstaller_explorer.yml | Image\|startswith: 'C:\Windows\Installer\Razer\Installer\' |
DRL 1.0 |
| sigma | proc_creation_win_susp_regedit_trustedinstaller.yml | title: Regedit as Trusted Installer |
DRL 1.0 |
| sigma | proc_creation_win_susp_run_folder.yml | - 'C:\Program Files (x86)\Microsoft Visual Studio\Installer\resources\app\ServiceHub\Services\Microsoft.VisualStudio.Setup.Service\BackgroundDownload.exe' |
DRL 1.0 |
| sigma | proc_creation_win_tap_installer_execution.yml | title: Tap Installer Execution |
DRL 1.0 |
| sigma | proc_creation_win_uac_cmstp.yml | description: Detect child processes of automatically elevated instances of Microsoft Connection Manager Profile Installer (cmstp.exe). |
DRL 1.0 |
| sigma | proc_creation_win_win_lolbas_dump64.yml | Image\|contains: '\Installer\Feedback\dump64.exe' |
DRL 1.0 |
| sigma | registry_event_asep_reg_keys_modification_currentversion.yml | Details: '"C:\Program Files\Zoom\bin\installer.exe" /repair' |
DRL 1.0 |
| sigma | registry_event_cmstp_execution_by_registry.yml | description: Detects various indicators of Microsoft Connection Manager Profile Installer execution |
DRL 1.0 |
| sigma | registry_event_runonce_persistence.yml | Details\|endswith: '\Installer\chrmstp.exe" --configure-user-settings --verbose-logging --system-level' |
DRL 1.0 |
| sigma | registry_event_vbs_payload_stored.yml | TargetObject\|contains: '\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\' |
DRL 1.0 |
| sigma | sysmon_always_install_elevated_msi_spawned_cmd_and_powershell_spawned_processes.yml | description: This rule looks for Windows Installer service (msiexec.exe) spawning command line and/or powershell that spawns other processes |
DRL 1.0 |
| sigma | sysmon_always_install_elevated_msi_spawned_cmd_and_powershell_spawned_processes.yml | - '\Windows\Installer\' |
DRL 1.0 |
| sigma | sysmon_always_install_elevated_parent_child_correlated.yml | description: This rule will looks any process with low privilege launching Windows Installer service (msiexec.exe) that tries to install MSI packages with SYSTEM privilege |
DRL 1.0 |
| sigma | sysmon_always_install_elevated_parent_child_correlated.yml | #look for child process from the suspicious_guid, alert if it's Windows Installer trying to install package with SYSTEM privilege |
DRL 1.0 |
| sigma | sysmon_always_install_elevated_parent_child_correlated.yml | - '\Windows\Installer\' |
DRL 1.0 |
| LOLBAS | Installutil.yml | Description: The Installer tool is a command-line utility that allows you to install and uninstall server resources by executing the installer components in specified assemblies |
|
| LOLBAS | Installutil.yml | - Link: https://docs.microsoft.com/en-us/dotnet/framework/tools/installutil-exe-installer-tool |
|
| LOLBAS | Ieadvpack.yml | Description: INF installer for Internet Explorer. Has much of the same functionality as advpack.dll. |
|
| malware-ioc | casbaneiro | \| F07932D8A36F3E36F2552DADEDAD3E22EFA7AAE1 \| MSI installer \| Win32/TrojanDownloader.Banload.YJD trojan |
© ESET 2014-2018 |
| malware-ioc | casbaneiro | \| 8745197972071EDE08AA9F7FBEC029BED56151C2 \| MSI installer \| JS/TrojanDownloader.Agent.TNX trojan |
© ESET 2014-2018 |
| malware-ioc | casbaneiro | \| DD2799C10954293C8E7D75CD4BE2686ADD9AC2D4 \| MSI installer \| JS/TrojanDownloader.Agent.TNX trojan |
© ESET 2014-2018 |
| malware-ioc | evilnum | ==== MSI installer |
© ESET 2014-2018 |
| malware-ioc | evilnum | \|AF12FD706F24B5296916FD85AF815541CC8FB810\|tvw32.exe \|Intel USB 3.0 installer \|22C4F55BBA23E9B886923784E7BAB8E95C33D823``{:.highlight .language-cmhg} |
© ESET 2014-2018 |
| malware-ioc | evilnum | \|0C8F24DAA4489329D0CDD4A82B3B45DAD14CA024\|nvstregs.exe \|Windows Installer Table Creator \|B2824928A60B3C129E257F16F41CDD5DD23659BE``{:.highlight .language-cmhg} |
© ESET 2014-2018 |
| malware-ioc | misp_invisimole.json | "value": "%APPDATA%\\Microsoft\\Installer\\kb043921.exe", |
© ESET 2014-2018 |
| malware-ioc | invisimole | %APPDATA%\Microsoft\Installer\kb043921.exe |
© ESET 2014-2018 |
| malware-ioc | invisimole | "command" = ""%APPDATA%\Microsoft\Installer\kb043921.exe" OpenFileMappingW 0xF003F 0 "XVD21x9DC" , MapViewOfFile $$:1 0xF003F 0 0 %installer_size% , CreateThread 0 0 $$:6 $$:6 0 0 , WaitForSingleObject $$:13 -1" |
© ESET 2014-2018 |
| malware-ioc | win_apt_invisimole_uac_bypass.yml | - '\Microsoft\Installer\kb043921.exe' |
© ESET 2014-2018 |
| malware-ioc | win_apt_invisimole_wdigest_chain.yml | - '\Microsoft\Installer\kb043921.exe' |
© ESET 2014-2018 |
| malware-ioc | mispadu | \| A4EDA0DD2C33A644FEEF170F5C24CF7595C19017 \| MSI installer \| VBS/TrojanDownloader.Agent.RVY |
© ESET 2014-2018 |
| malware-ioc | mispadu | \| CFE21DBFB97C2E93F099D351DE54099A3FC0C98B \| MSI installer \| VBS/TrojanDownloader.Agent.RVY |
© ESET 2014-2018 |
| malware-ioc | numando | \| 4A1C48064167FC4AD5D943A54A34785B3682DA92 \| MSI installer \| Win32/Spy.Numando.BA |
© ESET 2014-2018 |
| malware-ioc | oceanlotus | \|a40ee8ff313e59aa92d48592c494a4c3d81449af\|Firefox Installer.exe \|Win32/TrojanDropper.Agent.RUI |
© ESET 2014-2018 |
| malware-ioc | 2020_Q4 | \|9453E8DE98CE976744B1A4E133AA69BC8A5C523A\|Trojanized software installer \|Win32/InvisiMole.H |
© ESET 2014-2018 |
| malware-ioc | misp-ramsay.json | "comment": "Installer Launcher", |
© ESET 2014-2018 |
| malware-ioc | misp-ramsay.json | "comment": "Malware Installer", |
© ESET 2014-2018 |
| malware-ioc | misp-ramsay.json | "comment": "Ramsay Initial Installer", |
© ESET 2014-2018 |
| malware-ioc | misp-ramsay.json | "comment": "Initial Installer", |
© ESET 2014-2018 |
| malware-ioc | signsight-misp-event.json | "comment": "Trojanized installer", |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| udservice.exe \| update.ultimate-discounter[.]com |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| udservice.exe \| udiscount[.]net |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| udservice.exe \| ultimate-discounter[.]org |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| udservice.exe \| upd-discounter[.]com |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| udservice.exe \| udiscounter[.]org |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| udservice.exe \| wannaupdate[.]com |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| ghstore.exe \| ghosterystore[.]com |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| bhctrl32.exe \| nvccupdate[.]com |
© ESET 2014-2018 |
| malware-ioc | stantinko | \|Stantinko Installer \| redisd.exe \| rdsbase[.]com |
© ESET 2014-2018 |
| malware-ioc | misp-telebots.json | "comment": "Intercepter-NG and silent WinPCAP installer - Xchecked via VT: 64cb897acc37e12e4f49c4da4dfad606b3976225", |
© ESET 2014-2018 |
| malware-ioc | misp-telebots.json | "comment": "Intercepter-NG and silent WinPCAP installer", |
© ESET 2014-2018 |
| malware-ioc | telebots | === Intercepter-NG and silent WinPCAP installer |
© ESET 2014-2018 |
| malware-ioc | misp-mosquito-event.json | "comment": "Powershell backdoor installer", |
© ESET 2014-2018 |
| malware-ioc | misp-mosquito-event.json | "comment": "Installer", |
© ESET 2014-2018 |
| malware-ioc | turla | The blog post about Mosquito is available on WeLiveSecurity at https://www.welivesecurity.com/2018/01/09/turlas-backdoor-laced-flash-player-installer/. |
© ESET 2014-2018 |
| malware-ioc | vadokrist | \| D8C6DDACC42645DF0F760489C5A4C3AA686998A1 \| MSI installer \| JS/TrojanDownloader.Banload.ABD |
© ESET 2014-2018 |
| atomic-red-team | index.md | - T1574.005 Executable Installer File Permissions Weakness CONTRIBUTE A TEST | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - T1574.005 Executable Installer File Permissions Weakness CONTRIBUTE A TEST | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | | Visual Basic | Dynamic Linker Hijacking | Executable Installer File Permissions Weakness CONTRIBUTE A TEST | Disable or Modify System Firewall | Password Cracking | System Time Discovery | | | | Steganography CONTRIBUTE A TEST | | | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | | | Executable Installer File Permissions Weakness CONTRIBUTE A TEST | Hijack Execution Flow CONTRIBUTE A TEST | Domain Policy Modification CONTRIBUTE A TEST | Password Spraying | | | | | Web Service CONTRIBUTE A TEST | | | MIT License. © 2018 Red Canary |
| atomic-red-team | matrix.md | | | | LSASS Driver CONTRIBUTE A TEST | Local Accounts | Executable Installer File Permissions Weakness CONTRIBUTE A TEST | Steal Application Access Token CONTRIBUTE A TEST | | | | | | | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | | | Event Triggered Execution CONTRIBUTE A TEST | Executable Installer File Permissions Weakness CONTRIBUTE A TEST | Domain Controller Authentication CONTRIBUTE A TEST | Network Sniffing | System Owner/User Discovery | | Sharepoint CONTRIBUTE A TEST | | Non-Standard Port | | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | | | Executable Installer File Permissions Weakness CONTRIBUTE A TEST | Extra Window Memory Injection CONTRIBUTE A TEST | Domain Trust Modification CONTRIBUTE A TEST | Password Cracking | System Time Discovery | | Web Portal Capture CONTRIBUTE A TEST | | Port Knocking CONTRIBUTE A TEST | | | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-matrix.md | | | | Hypervisor CONTRIBUTE A TEST | Image File Execution Options Injection | Executable Installer File Permissions Weakness CONTRIBUTE A TEST | Password Managers CONTRIBUTE A TEST | Virtualization/Sandbox Evasion CONTRIBUTE A TEST | | | | Proxy CONTRIBUTE A TEST | | | MIT License. © 2018 Red Canary |
| atomic-red-team | T1040.md | | wireshark_url | wireshark installer download URL | Url | https://1.eu.dl.wireshark.org/win64/Wireshark-win64-latest.exe| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1046.md | | nmap_url | NMap installer download URL | Url | https://nmap.org/dist/nmap-7.80-setup.exe| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1056.002.md | Adversaries may mimic this functionality to prompt users for credentials with a seemingly legitimate prompt for a number of reasons that mimic normal usage, such as a fake installer requiring additional access or a fake malware removal suite.(Citation: OSX Malware Exploits MacKeeper) This type of prompt can be used to collect credentials via various languages such as AppleScript(Citation: LogRhythm Do You Trust Oct 2014)(Citation: OSX Keydnap malware) and PowerShell(Citation: LogRhythm Do You Trust Oct 2014)(Citation: Enigma Phishing for Credentials Jan 2015). </blockquote> | MIT License. © 2018 Red Canary |
| atomic-red-team | T1059.001.md | Write-Host Automated installer not implemented yet, please install PowerShell v2 manually | MIT License. © 2018 Red Canary |
| atomic-red-team | T1072.md | | radmin_installer | Radmin Viewer installer | Path | %TEMP%\RadminViewer.msi| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1072.md | echo Downloading radmin installer | MIT License. © 2018 Red Canary |
| atomic-red-team | T1113.md | | package_installer | Package installer command for linux. Debian system command- apt-get install x11-apps | String | yum install -y xorg-x11-apps| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1133.md | | chrome_url | chrome installer download URL | Url | https://dl.google.com/tag/s/appguid%3D%7B8A69D345-D564-463C-AFF1-A69D9E530F96%7D%26iid%3D%7BFD62DDBC-14C6-20BD-706F-C7744738E422%7D%26lang%3Den%26browser%3D3%26usagestats%3D0%26appname%3DGoogle%2520Chrome%26needsadmin%3Dprefers%26ap%3Dx64-stable-statsdef_1%26installdataindex%3Dempty/chrome/install/ChromeStandaloneSetup64.exe| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1135.md | | package_installer | Package installer command. Debian - apt install samba | String | (which yum && yum -y install epel-release samba)||(which apt-get && DEBIAN_FRONTEND=noninteractive apt-get install -y samba)| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1176.md | Once the extension is installed, it can browse to websites in the background,(Citation: Chrome Extension Crypto Miner)(Citation: ICEBRG Chrome Extensions) steal all information that a user enters into a browser (including credentials)(Citation: Banker Google Chrome Extension Steals Creds)(Citation: Catch All Chrome Extension) and be used as an installer for a RAT for persistence. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.003.md | <blockquote>Adversaries may abuse CMSTP to proxy execution of malicious code. The Microsoft Connection Manager Profile Installer (CMSTP.exe) is a command-line program used to install Connection Manager service profiles. (Citation: Microsoft Connection Manager Oct 2009) CMSTP.exe accepts an installation information file (INF) as a parameter and installs a service profile leveraged for remote access connections. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | <blockquote>Adversaries may use InstallUtil to proxy execution of code through a trusted Windows utility. InstallUtil is a command-line utility that allows for installation and uninstallation of resources by executing specific installer components specified in .NET binaries. (Citation: MSDN InstallUtil) InstallUtil is digitally signed by Microsoft and located in the .NET directories on a Windows system: C:\Windows\Microsoft.NET\Framework\v |
MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | | assembly_dir | directory to drop the compiled installer assembly | Path | $Env:TEMP\| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | | assembly_filename | filename of the compiled installer assembly | String | T1218.004.dll| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | CheckIfInstallable method execution test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | InstallHelper method execution test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | Executes the installer assembly class constructor. Upon execution, version information will be displayed the .NET framework install utility. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | InstallUtil class constructor execution test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | InstallUtil Install method execution test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | InstallUtil Uninstall method execution test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | InstallUtil HelpText property execution test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.004.md | Evasive Installutil invocation test failure. Installer assembly execution output did not match the expected output. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.007.md | <blockquote>Adversaries may abuse msiexec.exe to proxy execution of malicious payloads. Msiexec.exe is the command-line utility for the Windows Installer and is thus commonly associated with executing installation packages (.msi).(Citation: Microsoft msiexec) Msiexec.exe is digitally signed by Microsoft. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | An adversary may attempt to trick the user into downloading teamviewer and using this to maintain access to the machine. Download of TeamViewer installer will be at the destination location when sucessfully executed. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | An adversary may attempt to trick the user into downloading AnyDesk and use to establish C2. Download of AnyDesk installer will be at the destination location and ran when sucessfully executed. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | An adversary may attempt to trick the user into downloading LogMeIn and use to establish C2. Download of LogMeIn installer will be at the destination location and ran when sucessfully executed. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | An adversary may attempt to trick the user into downloading GoToAssist and use to establish C2. Download of GoToAssist installer will be at the destination location and ran when sucessfully executed. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | An adversary may attempt to trick the user into downloading ScreenConnect for use as a C2 channel. Download of ScreenConnect installer will be in the Downloads directory. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | $installer = “C:\Users$env:username\Downloads\ScreenConnect.msi” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | Invoke-WebRequest -OutFile $installer “https://d1kuyuqowve5id.cloudfront.net/ScreenConnect_21.11.4237.7885_Release.msi” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | msiexec /i $installer /qn | MIT License. © 2018 Red Canary |
| atomic-red-team | T1219.md | msiexec /x $installer /qn | MIT License. © 2018 Red Canary |
| atomic-red-team | T1546.011.md | A list of all shims currently installed by the default Windows installer (sdbinst.exe) is kept in: | MIT License. © 2018 Red Canary |
| atomic-red-team | T1550.002.md | Write-Host Automated installer not implemented yet, please install crackmapexec manually at this location: #{crackmapexec_exe} | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | $installer = “$env:temp\ChromeStandaloneSetup64.msi” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | msiexec /i $installer /qn | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | $installer = “$env:temp\OperaStandaloneInstaller.exe” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | Start-Process $installer -ArgumentList ‘/install /silent /launchopera=1 /setdefaultbrowser=0’ | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | $installer = “$env:temp\firefoxsetup.exe” | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | (New-Object Net.WebClient).DownloadFile($url,$installer) | MIT License. © 2018 Red Canary |
| atomic-red-team | T1555.003.md | Start-Process $installer -ArgumentList ‘/S’ -Wait | MIT License. © 2018 Red Canary |
| atomic-red-team | T1560.001.md | | rar_installer | Winrar installer | Path | %TEMP%\winrar.exe| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1560.001.md | echo Downloading Winrar installer | MIT License. © 2018 Red Canary |
| atomic-red-team | T1560.001.md | | 7zip_installer | 7zip installer | Path | %TEMP%\7zip.exe| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1560.001.md | echo Downloading 7-zip installer | MIT License. © 2018 Red Canary |
| atomic-red-team | T1562.001.md | | package_installer | Package installer command for linux. Default yum | String | (which yum && yum -y install epel-release rsyslog)||(which apt-get && apt-get install -y rsyslog)| | MIT License. © 2018 Red Canary |
| signature-base | apt_apt32.yar | description = “Detects APT32 installer side-loaded with goopdate.dll” | CC BY-NC 4.0 |
| signature-base | apt_grizzlybear_uscert.yar | $a1 = “Adobe Flash Player Installer” wide nocase | CC BY-NC 4.0 |
| signature-base | apt_hellsing_kaspersky.yar | description = “detection for Hellsing msger irene installer” | CC BY-NC 4.0 |
| signature-base | apt_kaspersky_duqu2.yar | $s2 = “Sysinternals installer” fullword wide /* PEStudio Blacklist: strings */ | CC BY-NC 4.0 |
| signature-base | apt_kaspersky_duqu2.yar | $s0 = “Installer for printer drivers and applications” fullword wide /* PEStudio Blacklist: strings */ | CC BY-NC 4.0 |
| signature-base | apt_ms_platinum.yara | description = “Installer component” | CC BY-NC 4.0 |
| signature-base | apt_ms_platinum.yara | description = “Installer for Dipsind variant” | CC BY-NC 4.0 |
| signature-base | apt_unc1151_ua.yar | $s2 = “CreateObject("WindowsInstaller.Installer")” | CC BY-NC 4.0 |
| signature-base | apt_wildneutron.yar | $s4 = “ Player Installer/Uninstaller” fullword wide /* PEStudio Blacklist: strings / / score: ‘11.42’ */ | CC BY-NC 4.0 |
| signature-base | apt_wildneutron.yar | $y1 = “Installer.exe” fullword ascii /* PEStudio Blacklist: strings / / score: ‘25.00’ */ | CC BY-NC 4.0 |
| signature-base | gen_anomalies_keyword_combos.yar | description = “Detects suspicious NullSoft Installer combination with common Copyright strings” | CC BY-NC 4.0 |
| signature-base | gen_dde_in_office_docs.yar | $r2 = “Adobe ARM Installer” | CC BY-NC 4.0 |
| signature-base | gen_maldoc.yar | description = “Triggers on docfiles executing windows installer. Used for deploying ThinBasic scripts.” | CC BY-NC 4.0 |
| signature-base | gen_maldoc.yar | $ = “WindowsInstaller.Installer$” | CC BY-NC 4.0 |
| signature-base | spy_equation_fiveeyes.yar | description = “Equation Group Malware - EquationDrug installer LUTEUSOBSTOS” | CC BY-NC 4.0 |
| signature-base | spy_equation_fiveeyes.yar | description = “Equation Group Malware - EquationLaser Installer” | CC BY-NC 4.0 |
| signature-base | thor-webshells.yar | rule installer { | CC BY-NC 4.0 |
| signature-base | thor-webshells.yar | description = “Webshells Auto-generated - file installer.cmd” | CC BY-NC 4.0 |
MIT License. Copyright (c) 2020-2021 Strontic.