InfDefaultInstall.exe
- File Path:
C:\WINDOWS\system32\InfDefaultInstall.exe - Description: INF Default Install
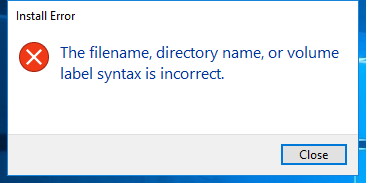
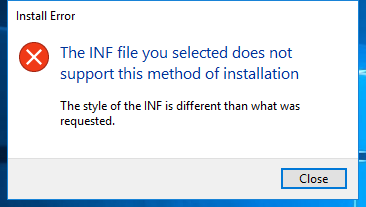
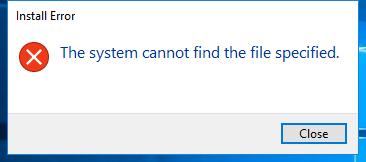
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 68D873F4D2C51EA4D0C02E77D7A5159C |
| SHA1 | 96CB6B29C3E337B1EFE805233C9A1A9498DF3964 |
| SHA256 | E6283D2406C9B31C9A1F98CFEA2C9B9DAF44EB3D9B86B52BD253D5F83D7FC14E |
| SHA384 | B848CB1CC6B93E231816A4695635B37443052C701F3FE9645B873D5918D74AA43629DC552313718F07E5CEFBDB23D69C |
| SHA512 | 349B54F5BAA78B27A67DD3E8C80D572641FE13DAA722977F335F1D8D9703C1A237891184360B1E5CC66C9F96392D602EFCA26E8BCC608E79F4B7BD08C7DD742E |
| SSDEEP | 192:y9qvExuDZMiPxMLDL0Zef6RDahWNsu5WEI3ZZUpYas9aW/GW:7vExKZdxMLgHWyWOpYacaW/GW |
| IMP | 85E247AC00016C5D35435F22FC7AB82E |
| PESHA1 | 1F6153C29AD77293BD6701848598B25A8997FA84 |
| PE256 | 117E6A97A9C746A2A2DCB2345418BEC569CA993AC7315A1E5E54519416F70EB0 |
Runtime Data
Loaded Modules:
| Path |
|---|
| C:\WINDOWS\system32\InfDefaultInstall.exe |
| C:\WINDOWS\System32\KERNEL32.DLL |
| C:\WINDOWS\System32\KERNELBASE.dll |
| C:\WINDOWS\System32\msvcp_win.dll |
| C:\WINDOWS\System32\msvcrt.dll |
| C:\WINDOWS\SYSTEM32\ntdll.dll |
| C:\WINDOWS\System32\shell32.dll |
Signature
- Status: Signature verified.
- Serial:
33000002ED2C45E4C145CF48440000000002ED - Thumbprint:
312860D2047EB81F8F58C29FF19ECDB4C634CF6A - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: InfDefaultInstall.EXE.MUI
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 5.2.3668.0
- Product Version: 5.2.3668.0
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 64-bit
File Scan
- VirusTotal Detections: 0/74
- VirusTotal Link: https://www.virustotal.com/gui/file/e6283d2406c9b31c9a1f98cfea2c9b9daf44eb3d9b86b52bd253d5f83d7fc14e/detection
File Similarity (ssdeep match)
| File | Score |
|---|---|
| C:\Windows\system32\InfDefaultInstall.exe | 30 |
| C:\WINDOWS\system32\InfDefaultInstall.exe | 29 |
| C:\Windows\system32\InfDefaultInstall.exe | 30 |
| C:\Windows\system32\InfDefaultInstall.exe | 33 |
Possible Misuse
The following table contains possible examples of InfDefaultInstall.exe being misused. While InfDefaultInstall.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_infdefaultinstall.yml | title: InfDefaultInstall.exe .inf Execution |
DRL 1.0 |
| sigma | proc_creation_win_infdefaultinstall.yml | - https://github.com/LOLBAS-Project/LOLBAS/blob/master/yml/OSBinaries/Infdefaultinstall.yml |
DRL 1.0 |
| sigma | proc_creation_win_infdefaultinstall.yml | - 'InfDefaultInstall.exe ' |
DRL 1.0 |
| LOLBAS | Infdefaultinstall.yml | Name: Infdefaultinstall.exe |
|
| LOLBAS | Infdefaultinstall.yml | - Command: InfDefaultInstall.exe Infdefaultinstall.inf |
|
| LOLBAS | Infdefaultinstall.yml | - Path: C:\Windows\System32\Infdefaultinstall.exe |
|
| LOLBAS | Infdefaultinstall.yml | - Path: C:\Windows\SysWOW64\Infdefaultinstall.exe |
|
| atomic-red-team | index.md | - Atomic Test #4: InfDefaultInstall.exe .inf Execution [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #4: InfDefaultInstall.exe .inf Execution [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | - Atomic Test #4 - InfDefaultInstall.exe .inf Execution | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | ## Atomic Test #4 - InfDefaultInstall.exe .inf Execution | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | Test execution of a .inf using InfDefaultInstall.exe | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | Reference: https://github.com/LOLBAS-Project/LOLBAS/blob/master/yml/OSBinaries/Infdefaultinstall.yml | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | | inf_to_execute | Local location of inf file | String | PathToAtomicsFolder\T1218\src\Infdefaultinstall.inf| | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | InfDefaultInstall.exe #{inf_to_execute} | MIT License. © 2018 Red Canary |
| atomic-red-team | T1218.md | Invoke-WebRequest “https://github.com/redcanaryco/atomic-red-team/raw/master/atomics/T1218/src/Infdefaultinstall.inf” -OutFile “#{inf_to_execute}” | MIT License. © 2018 Red Canary |
MIT License. Copyright (c) 2020-2021 Strontic.