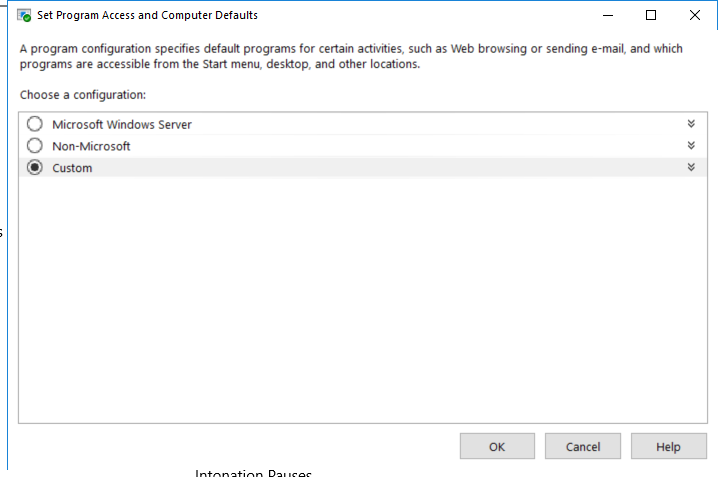
ComputerDefaults.exe
- File Path:
C:\windows\SysWOW64\ComputerDefaults.exe - Description: Set Program Access and Computer Defaults Control Panel
Screenshot
Hashes
| Type | Hash |
|---|---|
| MD5 | 1A506E36A76AD897490E77313CD3259A |
| SHA1 | E734173B941DB9E1260B78FAB6BF21DAF55915B4 |
| SHA256 | 2990059766F4118256B48DECFE2D586D469A219C1E5DDA038943C97BBFAA661D |
| SHA384 | D97335966E1BB6A92D36F1FD153E7FE752E83253CA98FCE0D8A68A53B1E7212E5607472CDED04F06D0500094909C8AE0 |
| SHA512 | DDA7ABC50BE919FFF6E0133FA3C47DCCE92ED82109F3709A3EA79D37E028FC2F99656028367AFC8D19D0D86867A4F301B7946CCD1792824322C901E155350E33 |
| SSDEEP | 768:u7Q6e6JTWs2IkRDzsq4ytZZZL2YCX4ibRY:u75fBURDoq4OZZZLlCIibR |
Signature
- Status: The file C:\windows\SysWOW64\ComputerDefaults.exe is not digitally signed. You cannot run this script on the current system. For more information about running scripts and setting execution policy, see about_Execution_Policies at http://go.microsoft.com/fwlink/?LinkID=135170
- Serial: ``
- Thumbprint: ``
- Issuer:
- Subject:
File Metadata
- Original Filename: ComputerDefaults.EXE.MUI
- Product Name: Microsoft Windows Operating System
- Company Name: Microsoft Corporation
- File Version: 6.3.9600.16384 (winblue_rtm.130821-1623)
- Product Version: 6.3.9600.16384
- Language: English (United States)
- Legal Copyright: Microsoft Corporation. All rights reserved.
File Similarity (ssdeep match)
Possible Misuse
The following table contains possible examples of ComputerDefaults.exe being misused. While ComputerDefaults.exe is not inherently malicious, its legitimate functionality can be abused for malicious purposes.
| Source | Source File | Example | License |
|---|---|---|---|
| sigma | proc_creation_win_uac_bypass_computerdefaults.yml | title: UAC Bypass Using ComputerDefaults |
DRL 1.0 |
| sigma | proc_creation_win_uac_bypass_computerdefaults.yml | description: Detects the pattern of UAC Bypass using computerdefaults.exe (UACMe 59) |
DRL 1.0 |
| sigma | proc_creation_win_uac_bypass_computerdefaults.yml | Image: 'C:\Windows\System32\ComputerDefaults.exe' |
DRL 1.0 |
| sigma | registry_event_shell_open_keys_manipulation.yml | description: Detects the shell open key manipulation (exefile and ms-settings) used for persistence and the pattern of UAC Bypass using fodhelper.exe, computerdefaults.exe, slui.exe via registry keys (e.g. UACMe 33 or 62) |
DRL 1.0 |
| atomic-red-team | index.md | - Atomic Test #5: Bypass UAC using ComputerDefaults (PowerShell) [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | windows-index.md | - Atomic Test #5: Bypass UAC using ComputerDefaults (PowerShell) [windows] | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | - Atomic Test #5 - Bypass UAC using ComputerDefaults (PowerShell) | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | ## Atomic Test #5 - Bypass UAC using ComputerDefaults (PowerShell) | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | PowerShell code to bypass User Account Control using ComputerDefaults.exe on Windows 10 | MIT License. © 2018 Red Canary |
| atomic-red-team | T1548.002.md | Start-Process “C:\Windows\System32\ComputerDefaults.exe” | MIT License. © 2018 Red Canary |
MIT License. Copyright (c) 2020-2021 Strontic.